CloudEyE’s intital stage is a downloader that spreads via #PowerShell scripts, #JavaScript files, and #NSIS executables . These download the next stage – the cryptor component – with the final payload packed within. All of the CloudEyE stages are heavily obfuscated.
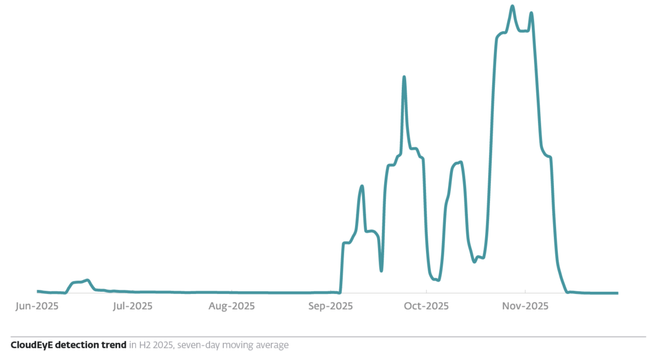
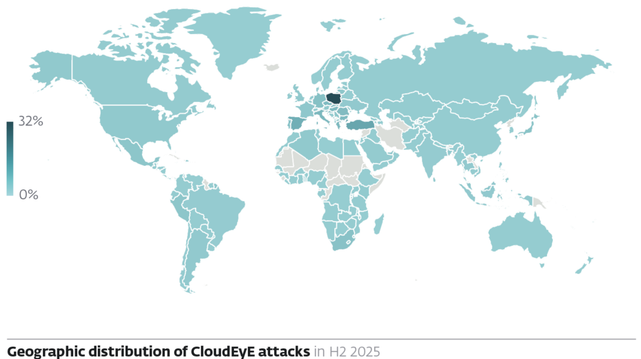
Most of CloudEyE attack attempts we registered in H2 2025 targeted Poland (32%). These attacks were part of a wave of email campaigns in Central and Eastern Europe ESET observed in September and October 2025.
In order to appear legitimate, the emails deployed in the campaign were often sent from compromised legitimate accounts and localized to the language of the targeted country. They were usually inquiries about invoice payments, package tracking, and purchase orders.
For further information on CloudEyE, cryptors, and more, head on over to the latest #ESETThreatReport: https://web-assets.esetstatic.com/wls/en/papers/threat-reports/eset-threat-report-h22025.pdf