Ok Ive been working through the mitigations for the string of kernel vulnerabilities. I think this is all of them. I had Claude spit out a summary.
Hope this helps others.
Linux Kernel LPE Roundup — May 7, 2026
Four local privilege escalation vulnerabilities in the same bug class (page-cache writes) are actively circulating. Here’s what you need to know:
1. Copy Fail (CVE-2026-31431)
Original page-cache write via algif_aead in the crypto subsystem. Patched upstream, distro patches available.
Mitigation: Blacklist algif_aead module, or apply your distro’s kernel update.
https://copy.fail/
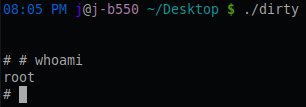
2. Dirty Frag (no CVE yet)
Chains xfrm-ESP + RxRPC page-cache writes for a universal unprivileged LPE across all major distros. Published after a third party broke the embargo — no patches exist yet.
Mitigation: Blacklist esp4, esp6, and rxrpc modules.
https://github.com/V4bel/dirtyfrag/
3. Copy Fail 2: Electric Boogaloo (no CVE yet)
xfrm ESP-in-UDP variant using MSG_SPLICE_PAGES. Same class as Copy Fail, different subsystem. Autoloads esp4/xfrm modules via userns netlink. Upstream fix committed but not yet in stable branches.
Mitigation: Blacklist esp4 (same as Dirty Frag).
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
4. io_uring ZCRX Freelist LPE (no CVE yet)
Out-of-bounds write in io_uring’s zero-copy receive freelist. Narrower scope — requires kernel 6.15+, CONFIG_IO_URING_ZCRX=y, a supported NIC (mlx5/ice/nfp), and CAP_NET_ADMIN. Fix committed but not in stable yet.
Mitigation: Check grep CONFIG_IO_URING_ZCRX /lib/modules/$(uname -r)/config — if not set, you’re not affected.
https://ze3tar.github.io/post-zcrx.html
#linux #kernel #cve #vulnerability #copyfail #copyfail2 #dirtyfrag #security #infosec #sysadmin