New Linux LPE, 5.10 and above (ptrace_may_access mm-NULL + pidfd_getfd)
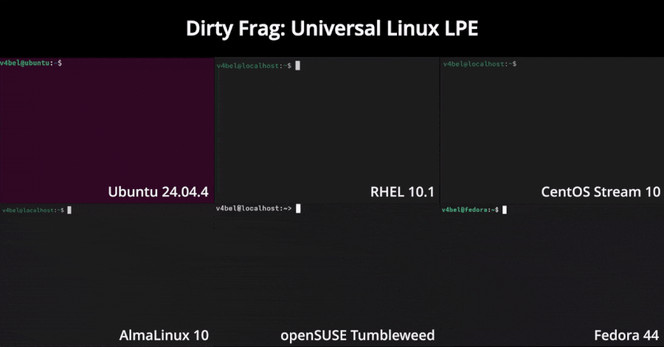
리눅스 커널 5.10 이상 버전에서 발견된 로컬 권한 상승(LPE) 취약점은 __ptrace_may_access() 함수가 task->mm가 NULL일 때 dumpable 체크를 건너뛰는 점을 악용합니다. 이로 인해 비권한 사용자가 pidfd_getfd()를 통해 루트 권한 파일인 SSH 호스트 키와 /etc/shadow 파일을 탈취할 수 있습니다. 해당 취약점은 6년 전부터 알려졌으며, Qualys가 보고하고 Linus Torvalds가 2026년 5월 14일에 패치했습니다. 여러 주요 리눅스 배포판에서 영향을 받으며, 공개된 PoC 코드를 통해 실제 공격 재현이 가능합니다.
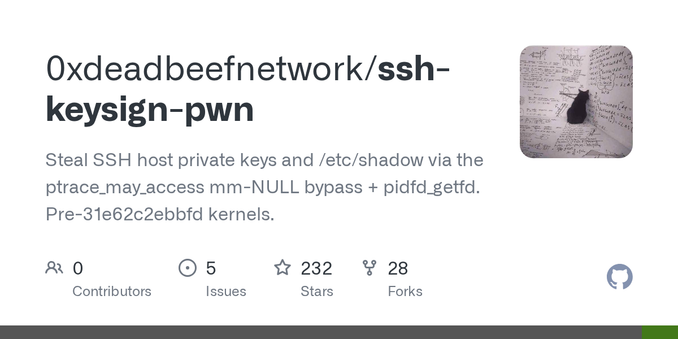
GitHub - 0xdeadbeefnetwork/ssh-keysign-pwn: Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels.
Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels. - 0xdeadbeefnetwork/ssh-keysign-pwn