#copyfail #copyfail2 #pack2theroot #dirtyfrag #Lineageos #Android
#copyfail #copyfail2 #pack2theroot #dirtyfrag #Lineageos #Android
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
🥷🐧 Дослідники з інформаційної безпеки виявили ще дві серйозні LPE-вразливості в #Linux: #CopyFail2: Electric Boogaloo та #DirtyFrag.
Ці вразливості дають змогу непривілейованому локальному користувачу отримати root-доступ до системи.
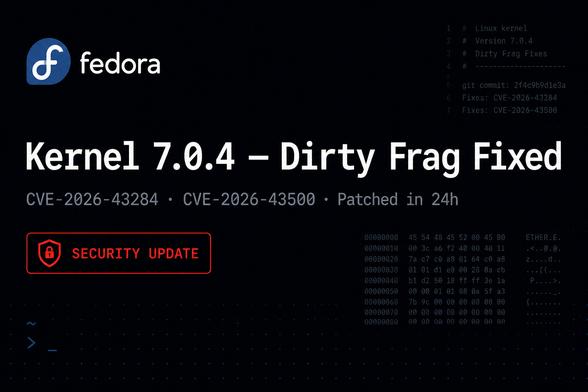
Fedora pushed kernel 7.0.4 to stable to fix the Dirty Frag and Copy Fail 2 vulnerabilities. Both CVE-2026-43284 and CVE-2026-43500 Patched.
Full details here: https://ostechnix.com/fedora-44-kernel-7-0-4-dirty-frag-copy-fail-2-fix/
#Fedora44 #Linuxkernel704 #DirtyFrag #CopyFail2 #CVE_2026_43284 #CVE_2026_43500
And here's another one:
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
This one is not fixed by f4c50a40, so all current kernels are vulnerable. Looks like mitigation is possible by blocking kernel modules `esp4` + `esp6` here as well (and breaking #IPSec in doing so). Can someone confirm?
Why is it called "Electric Boogaloo"… is this a #DonaldByrd fan? Were they inspired by this week's @thekalimerashow shows??
#privilegeescalation #linux #vulnerability #linuxadmin #sysadmin #exploit #copyfail2 #electricboogaloo
And there’s Copyfail2 on the way:
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
Ok Ive been working through the mitigations for the string of kernel vulnerabilities. I think this is all of them. I had Claude spit out a summary.
Hope this helps others.
NOTE: I have edited this post to better outline the fixes and improve terminology. Plus we've got a CVE designation for dirty frag now.
## Linux Kernel LPE Roundup — May 8, 2026
Four local privilege escalation vulnerabilities in the same bug class (page-cache writes) are actively circulating. Here's what you need to know:
### 1. Copy Fail (CVE-2026-31431)
Original page-cache write via algif_aead in the crypto subsystem. Patched upstream, distro patches available.
Mitigation: Apply your distro's kernel update, or prevent the module from loading:
echo 'install algif_aead /bin/false' > /etc/modprobe.d/copyfail.conf
### 2. Dirty Frag (CVE-2026-43284)
Chains xfrm-ESP + RxRPC page-cache writes for a universal unprivileged LPE across all major distros. Published after a third party broke the embargo — no patches exist yet.
Mitigation: Prevent the modules from loading:
printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf
Then unload them if currently loaded:
rmmod esp4 esp6 rxrpc 2>/dev/null
https://github.com/V4bel/dirtyfrag/
### 3. Copy Fail 2: Electric Boogaloo (no CVE yet)
xfrm ESP-in-UDP variant using MSG_SPLICE_PAGES. Same class as Copy Fail, different subsystem. Autoloads esp4/xfrm modules via userns netlink. Upstream fix committed but not yet in stable branches.
Mitigation: Same esp4 modprobe override as Dirty Frag covers this.
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
### 4. io_uring ZCRX Freelist LPE (no CVE yet)
Out-of-bounds write in io_uring's zero-copy receive freelist. Narrower scope — requires kernel 6.15+, CONFIG_IO_URING_ZCRX=y, a supported NIC (mlx5/ice/nfp), and CAP_NET_ADMIN. Fix committed but not in stable yet.
Mitigation: Check if you're affected:
grep CONFIG_IO_URING_ZCRX /lib/modules/$(uname -r)/config
No output or "is not set" means you're not vulnerable.
https://ze3tar.github.io/post-zcrx.html
### Note
If any of these modules are built into your kernel (=y rather than =m), the modprobe approach won't work — you'll need initcall_blacklist= on the kernel command line instead. Check with:
grep -E 'CONFIG_INET_ESP=|CONFIG_INET6_ESP=|CONFIG_AF_RXRPC=|CONFIG_CRYPTO_USER_API_AEAD=' /lib/modules/$(uname -r)/config
#linux #kernel #cve #vulnerability #copyfail #copyfail2 #dirtyfrag #security #infosec #sysadmin
HackerNewsBot (@[email protected])
Dirtyfrag: Universal Linux LPE https://news.ycombinator.com/item?id=48053623 #hackernews #tech