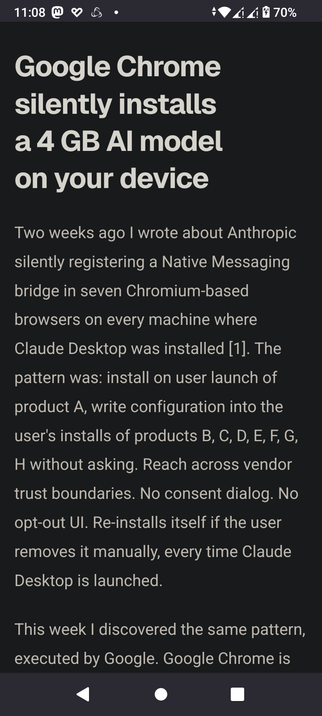
No consent dialog. No opt-out UI. Re-installs itself if the user removes it manually
Chrome is now LLM malware
Chrome on all OS, silently installs an LLM on your local machine, (like) true authentic malware. It's 2 to 4 GB 4096MB in size, taking up space I'm certain you have reserved for something else.
No consent dialog. No opt-out UI. Re-installs itself if the user removes it manually.
Google transformed Chrome into malware
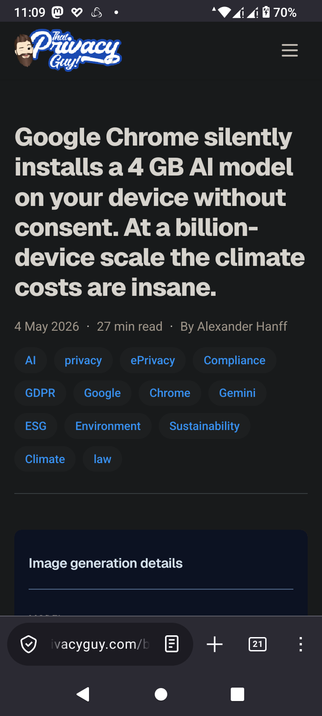
With billions 109 installations, the climate burden is Massive!
https://www.thatprivacyguy.com/blog/chrome-silent-nano-install/
#Distributed #malware #Alphabet #Google #Chrome #silent #re #install #botnet #LLM #AI #Slop #Enshittification #programming #virus #fucked