🎯 NOW PUBLISHING: On-Location Coverage from #BlackHat USA 2025!
We're back in the office and excited to start sharing all the conversations we captured on location in Las Vegas with our amazing sponsors and editorial coverage!
🔔 Follow ITSPmagazine, Sean Martin, CISSP, and Marco Ciappelli to get this content fresh as it drops!
We're thrilled to share this critical Brand Story conversation thanks to our friends at ReversingLabs 🙏
Your Business Apps Are Bringing Friends You Didn't Invite
Every commercial software application is a complex assembly of first-party, contracted, open source, and third-party code. But when #SolarWinds, #Kaseya, and #Ivanti happened, we learned that vendor questionnaires and contractual assurances offer little protection against supply chain compromises.
At #BlackHat2025, Saša Zdjelar, Chief Trust Officer at ReversingLabs, reveals how organizations can finally verify the integrity of #software from outside vendors—without relying on blind trust.
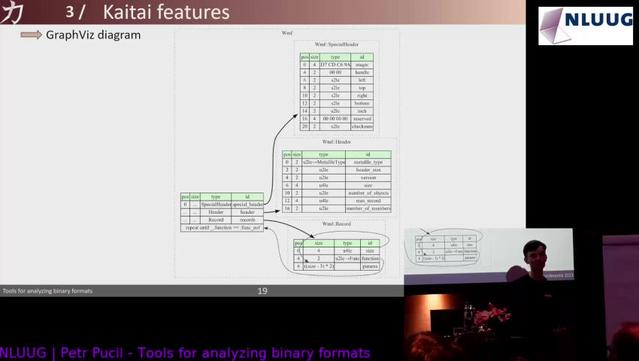
The game-changer: Comprehensive binary analysis that deconstructs any file into its components to:
• Detect malware, tampering, and embedded secrets
• Identify #vulnerabilities and insecure practices
• Uncover undocumented network connections
• Flag #compliance risks from restricted regions
This isn't just another policy checkbox—it's a true technical control that inspects the software itself, regardless of size or complexity.
Real-world applications:
• Procurement: Auto-scan all software before deployment
• Version Monitoring: Detect unexpected behavior changes between releases
• Critical Environments: Verify integrity before software enters OT, ICS, or financial systems
• Risk Management: Assess COTS software as part of ongoing vendor reviews
With regulations like EO 14028 and the EU's #CyberResilience Act demanding transparency, the ability to technically validate every application delivers both strategic protection and measurable benefits.
📺 Watch the video: https://youtu.be/pU9bHYFND7c
🎧 Listen to the podcast: https://brand-stories-podcast.simplecast.com/episodes/your-business-apps-are-bringing-friends-you-didnt-invite-a-brand-story-with-saa-zdjelar-chief-trust-officer-at-reversinglabs-and-operating-partner-at-crosspoint-capital-a-black-hat-usa-2025-conference-on-location-brand-story-a2sfPy_B
📖 Read the blog: https://www.itspmagazine.com/their-stories/your-business-apps-are-bringing-friends-you-didnt-invite-a-brand-story-with-saa-zdjelar-chief-trust-officer-at-reversinglabs-a-black-hat-usa-2025-on-location-brand-story
➤ Learn more about ReversingLabs: https://itspm.ag/reversinglabs-v57b
✦ Catch more stories from #ReversingLabs: https://www.itspmagazine.com/directory/reversinglabs
🎪 Follow all of our #BHUSA 2025 coverage: https://www.itspmagazine.com/bhusa25
#Cybersecurity #SupplyChainSecurity #SoftwareIntegrity #BlackHatUSA #BHUSA25 #ThirdPartyRisk #SBOM #BinaryAnalysis #Compliance #ZeroTrust