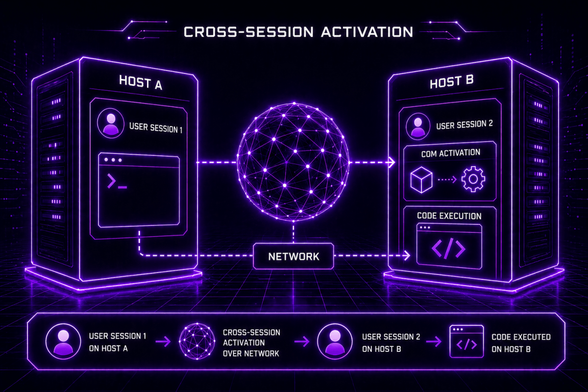
🚨 Cross‑Session Activation is a detection gap hiding in plain sight.
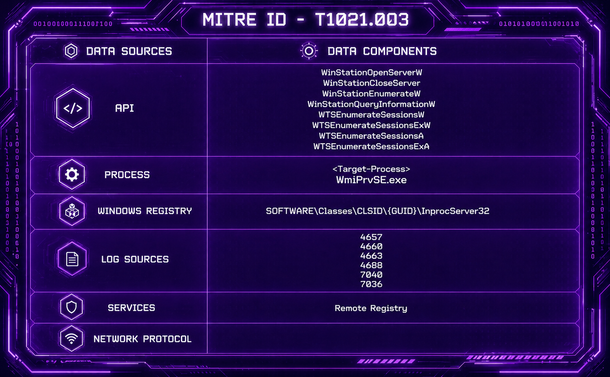
💡 The technique abstract below highlights the minimum viable signals for defenders.
💭 Interesting to know if this technique is part of your threat emulation library.
📉 𝐂𝐲𝐛𝐞𝐫 𝐬𝐢𝐠𝐧𝐚𝐥 𝐢𝐬 𝐝𝐫𝐨𝐩𝐩𝐢𝐧𝐠.
📈 𝐀𝐈 𝐧𝐨𝐢𝐬𝐞 𝐢𝐬 𝐫𝐢𝐬𝐢𝐧𝐠.
To help, I created a list of active cybersecurity blogs written by people who still publish real research.
If you follow any of these already (or have gems I should add), let me know.
📌https://github.com/netbiosX/CyberSec-Blogs #redteam #purpleteam #threathunting

GitHub - netbiosX/CyberSec-Blogs: Lists of independent cybersecurity blogs covering threat intelligence, purple team, red team, threat hunting, and detection engineering. Most are personal blogs maintained by practitioners who publish original research, tradecraft, and tooling.
Lists of independent cybersecurity blogs covering threat intelligence, purple team, red team, threat hunting, and detection engineering. Most are personal blogs maintained by practitioners who publ...
Accidentally leveraged a supply chain attack this week when it turned out that the GitHub org I'd cloned for a cyber exercise was "unofficial" and none of the exercise participants knew who actually owned it although they did recognise the committers. Chaos ensued.
I have made some recent updates to my Ultimate Cybersecurity Guide GitHub Repo! New documentation, new how-to guides and new subsections to the AI portion of the repo, as well as a few other things here and there. Give it a look if you are at all interested!
#GitHub #Cybersecurity #Guide #HowTo #PurpleTeam https://github.com/Pnwcomputers/ULTIMATE-CYBERSECURITY-MASTER-GUIDE
GitHub - Pnwcomputers/ULTIMATE-CYBERSECURITY-MASTER-GUIDE: This repository provides a centralized resource for operational cyber defense and offense, compiling Theory, Tools, Operating Procedures, and Step-by-Step Guides across various critical security domains. Content is sourced from industry-leading books and technical presentations, focusing on practical application rather than JUST theory.
This repository provides a centralized resource for operational cyber defense and offense, compiling Theory, Tools, Operating Procedures, and Step-by-Step Guides across various critical security do...
We are looking for Talks, Workshops, Tool Demos, and Hands-on Activities focused strictly on adversary simulation, threat emulation, offensive tradecraft, threat-informed defense, offensive cyber security, state-sponsored threat actors, purple teaming, and real-world attacker techniques. Vendor-neutral, technical, and practical content only.
Submit your research here: https://adversaryvillage.org/call-for-papers/
CFP Closes on: 31st May 2026
#DEFCON34 #AdversaryVillage
#OffensiveCyberSecurity #AdversarySimulation #PurpleTeam #ThreatActors #Breaches #DEFCON
Another talk announcement for BSides Luxembourg!
🔥🤖 𝗢𝗛 𝗦𝗛𝗜𝗧 𝗜 𝗔𝗖𝗖𝗜𝗗𝗘𝗡𝗧𝗔𝗟𝗟𝗬 𝗕𝗥𝗘𝗔𝗖𝗛𝗘𝗗 𝗔𝗡 𝗢𝗥𝗚𝗔𝗡𝗜𝗭𝗔𝗧𝗜𝗢𝗡 (𝗢𝗥 𝗠𝗔𝗡𝗬) 𝗨𝗦𝗜𝗡𝗚 𝗔𝗜 – Panagiotis Fiskilis 💥
What starts as a harmless search can spiral into a multi-organization data breach—especially when AI gets involved.
This talk dives into real-world research showing how AI can be weaponized for OSINT, enabling large-scale data discovery, spear phishing campaigns, and even manipulation of AI systems themselves. From injecting malicious context into models to scaling attacks via APIs and agent workflows, this session explores how adversaries can turn AI into a powerful offensive tool—and how defenders can detect and respond.
Expect a true purple team perspective, blending attacker techniques with defensive insights, including OPSEC considerations and strategies to identify malicious AI-driven activities before they escalate.
Panagiotis Fiskilis is a Senior Red Team Operator at NVISO, specializing in API hacking, Active Directory exploitation, and malware development. With multiple industry certifications (OSCP, OSWE, CRTO, eWPT and more), he brings hands-on offensive expertise combined with a strong research-driven mindset.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule Link: https://pretalx.com/bsidesluxembourg-2026/schedule/
👉 Browse sessions, track talks in real time, and plan your schedule on Hacker Tracker: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #AISecurity #RedTeam #OSINT #CyberSecurity #AI #ThreatIntelligence #PurpleTeam
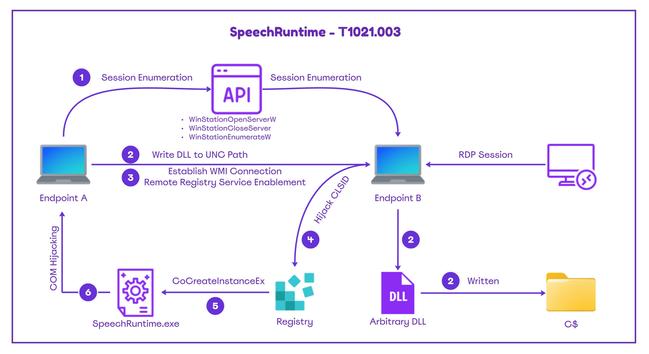
This diagram summarizes the chain.⤵️
🖊️ https://ipurple.team/2026/04/07/microsoft-speech/ #purpleteam
📢 New Article: Lateral Movement via Microsoft Speech
🎙️ Microsoft Speech Platform is built-in in Windows environments to enable Speech recognition, Voice input, Text-to-Speech & Speech features in Windows, Edge & Office
🦄 Deep‑dive playbook on how Microsoft Speech can be abused for lateral movement and how defenders can perform detection.
📖 1x Playbook
💡 Detection Opportunities
🏹 1x MDE Query
𝐃𝐞𝐭𝐞𝐜𝐭𝐢𝐨𝐧 - 𝐄𝐯𝐞𝐧𝐭 𝐈𝐃'𝐬
✅️ 4657 & 4663 - {655D9BF9-3876-43D0-B6E8-C83C1224154C}
✅️ 4688 - SpeechRuntime.exe
✅️ 7040 & 7036 - RemoteRegistry Service
✒️ https://ipurple.team/2026/04/07/microsoft-speech/ #purpleteam #blueteam #detectionengineering
Another talk announcement!
🟣🤖 𝗚𝗢𝗢𝗗𝗕𝗬𝗘 𝗣𝗨𝗥𝗣𝗟𝗘 𝗧𝗘𝗔𝗠, 𝗛𝗘𝗟𝗟𝗢 𝗣𝗨𝗥𝗣𝗟𝗘 𝗕𝗢𝗧𝗦 - 𝗣𝗔𝗧𝗥𝗜𝗖𝗞 𝗠𝗞𝗛𝗔𝗘𝗟 & 𝗥𝗔𝗟𝗣𝗛 𝗘𝗟 𝗞𝗛𝗢𝗨𝗥𝗬 🛡️⚔️
What if purple teaming could run itself? 🚀 This talk reveals an AI driven framework that simulates real world attacks, uncovers detection gaps, and continuously strengthens your defenses with zero manual effort. It's more than automation. It is a smart, self evolving security cycle where offense and defense work together in real time to stay ahead of threats.
Patrick Mkhael https://pretalx.com/bsidesluxembourg-2026/speaker/WHMGFD/ is an Offensive Security R&D lead with a strong blue team foundation, now focused on red teaming, cloud pentesting, and building tools for adversary emulation and automated security testing.
Ralph El Khoury https://pretalx.com/bsidesluxembourg-2026/speaker/X9QCJN/ is a red teamer and CVE hunter with a passion for breaking AD and web apps. Teaches kids to question everything, starting with default credentials.
📅 Conference dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule Link: https://pretalx.com/bsidesluxembourg-2026/schedule/
#BSidesLuxembourg2026 #CyberSecurity #PurpleTeam #RedTeam #BlueTeam #AI