| Website | https://www.radare.org |
| GitHub | https://github.com/radareorg/radare2 |
| Discord | https://discord.gg/YBey7CR9jf |
| Conference (Oct 24,25) | https://radare.org/con |
 radare
radare 
- 1.9K Followers
- 2 Following
- 1.2K Posts
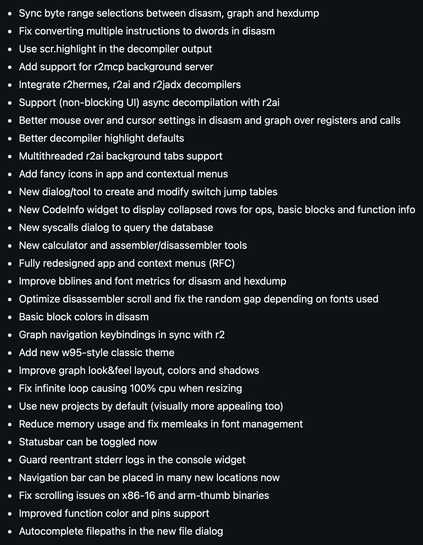
💥 iaito 6.1.6 release notes are massive! 💥
Now it's time for packagers and distros to bring all those goods to the users \o/ https://github.com/radareorg/iaito/releases/tag/6.1.6
RE: https://infosec.exchange/@radareorg/116683791203835130
Some of the improvements I did in r2 were driven to make iaito (the desktop app) a first class citizen in r2land, but also to reduce friction with r2mcp merging api helpers upstream.. and more importantly for r2flutter 👈 which will be released soon in sync with my @owasp conference presentation
💥 iaito 6.1.6 release notes are massive! 💥
Now it's time for packagers and distros to bring all those goods to the users \o/ https://github.com/radareorg/iaito/releases/tag/6.1.6
⚠️Don’t get fooled by the version numbers in radare2. We don’t follow the semver rules, in r2land we use odd numbers to refer to unstable/development versions. If you care about abi breaks use the R2_ABIVERSION which will quickly point you to the specific change in apis or structs and its independent from release tags.
A small release like 6.1.4 -> 6.1.6 packs almost 500 commits and 24 abi changes.
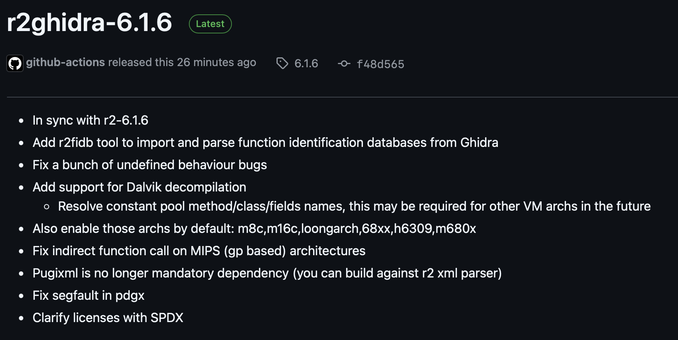
📦radare2-6.1.6 codename “lospatos2”
- improved local variable analysis
- introduce dynamic calling conventions dsl
- better stack argument tracking, support multireturn pairs
- redesigned jump table analysis (afbt command), fixes rust and dex switch statements
- safer, faster and use less memory parsing binaries (30%)
- extended swift/objc support
- bump PPC emulation and analysis
- store types, local vars, callconvs and xrefs in new projects