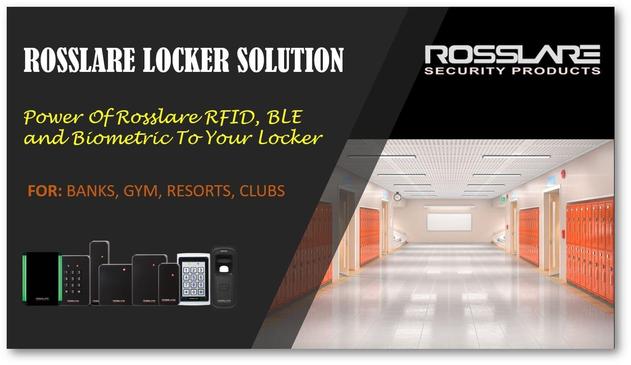
Upgrade from traditional locks to smart access control 🔑
Rosslare offers scalable and secure solutions for modern businesses.
📞 Contact SARC Infosolution
📱 +91-9594283444
📧 [email protected]
📢 WhatsApp Channel: https://zurl.co/tmzeQ
Finalizing the slides for today’s session on Zero Trust controls. PAM is often the missing piece of the puzzle for many orgs. Looking forward to breaking down how to limit the "blast radius" when things go sideways. 💥🛡️
See you there!
#CyberSecurity #InfoSec #ZeroTrust #PAM #AccessControl #TechPost
Security is no longer optional — it’s critical.
With Rosslare Access Control Systems, ensure only authorized access across your facility.
✔️ Smart Controllers
✔️ RFID & Biometric Integration
✔️ Centralized Monitoring
📞 Contact SARC Infosolution
📱 +91-9594283444
📧 [email protected]
📢 WhatsApp Channel: https://zurl.co/k3gHX
#AccessControl #Rosslare #SecuritySolutions #SmartSecurity #SARC #SARCInfosolution
Secure IAM onboarding prevents hidden risks, access gaps using standardized processes, RBAC, continuous monitoring. Infosec K2K streamlines workflows, controls.
#CyberSecurity #IAM #IdentitySecurity #AccessControl #ZeroTrust #IAMOnboarding #CyberResilience #InfosecK2K
TechRadar (@techradar)
AI 에이전트의 빠른 도입이 적절한 보안 장치 없이 진행되면서 시스템 노출, 데이터 위험, 접근 제어 악용 가능성이 커지고 있다는 경고다. AI 개발과 운영에서 보안 가드레일의 중요성을 강조한다.
Identity-based attacks are increasing across enterprises. Strong IAM and access controls are critical. Infosec K2K strengthens identity security with adaptive protection.
#CyberSecurity #IdentitySecurity #IAM #ZeroTrust #AccessControl #InfosecK2K
Identity Management Day is a reminder that controlling who has access to your systems is just as important as protecting them.
Reviewing user access, using strong passwords, and enabling multi-factor authentication can help reduce risk and prevent unauthorized access.
#SimplifiedITConsulting #YourITSimplified #CyberSecurity #AccessControl
🔐 Cyber Tip: Regularly audit admin accounts for unauthorized access.
Limit who has elevated privileges and remove access that is no longer required. Admin accounts are prime targets.