Malware detection is a constant arms race where the methods for identifying malicious pieces of code must keep up with the ways their disseminators are able to conceal their nature. In the newly published paper “Multimodal Malware Detection under Obfuscated and Adversarial Attack Conditions Using ResNet-50 and MLP Encoders with Contrastive Learning and Adaptive Cross-Modal Fusion” Peter Sackitey, Collinson Colin Mawunyo Agbesi, and Timothy Graham present promising results of a hybrid approach that combines methods of analysis of Android APK files represented both as images and in a tabular form.
The article is available on ACIG’s website: https://www.acigjournal.com/Multimodal-Malware-Detection-under-Obfuscated-and-Adversarial-Attack-Conditions-Using,219075,0,2.html
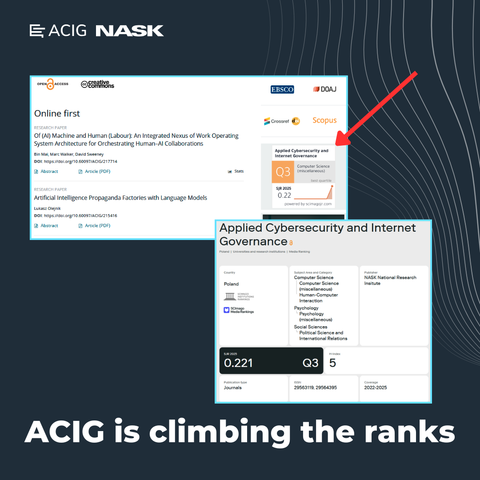
🌐 Applied Cybersecurity & Internet Governance (#ACIG) is published by #NASK – National Research Institute
#malware #malwareDetection #MLP #ResNet-50 #Android #APK