How has the #OSINT landscape evolved over the past half-decade, a period of immense geopolitical, societal, and digital change & disruption across the globe?
I just published an original analysis on the topic, a data-driven study derived from 5+ years of tracking thousands of #opensource #intelligence research tools & resources: https://metaosint.github.io/2023-osint-trends-analysis.html
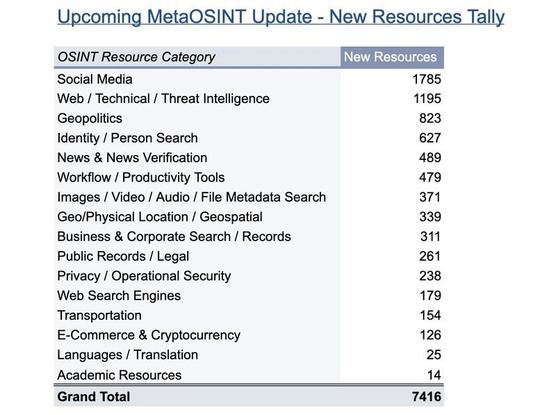
The MetaOSINT project launched in 2021 as a tactical aide for researchers & investigators (explore the free tool’s two main features here: https://metaosint.github.io/). But after publishing multiple updates since, including a huge set of additions last month, it felt worthwhile to examine how shifts in the dataset might be reflecting broader trends & changes in the underlying information landscape
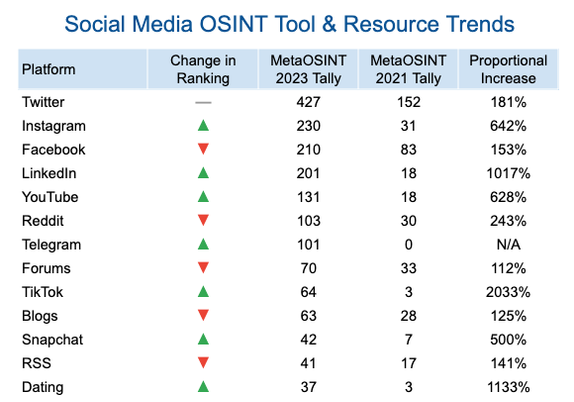
Key themes in the piece include social media OSINT trends, geopolitical resources (Russia, Ukraine, & more), and large increases in #disinformation & #verification tools and accountability projects. I know there are many more insights to be gleaned from the data, which is all publicly available, so be sure to let me know what you find after digging in 🔎
#MetaOSINT #intelligenceanalysis #dataviz #datascience #socmint #geoint #imint #darkweb #digitalprivacy