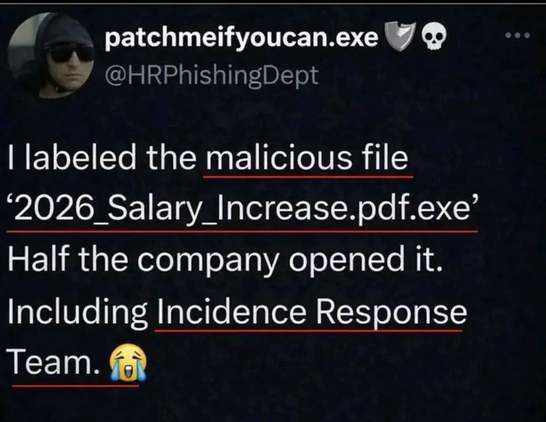
it doesn't help that some bad operating systems hide the file extension.
nor that people are really fucking stupid lol
@DigitalInfinity @bazkie @nixCraft
Companies don't want to pay for skilled admins that know this is a reasonable thing to do (or even possible!)
Management failure
@bazkie The targets don't even know, what a file extension is.
This "company" has no IT security, that's the problem. Security costs money and is invisible to the management.
Why the fuck does the mail server accept EXE?
Why the fuck has the mail client no filter?
Why the fuck are there no execution restrictions?
It's not the users fault.
@nixCraft
Well I guess "Thanks Windows for masking file extensions by default" ? 🤷♂️
@nixCraft laugh
I'm not surprised. A few years ago I heard someone say, "My most successful attacks are still just poorly written powershells."
If users don't care, no amount of security will protect them.
our biggest problem is in human shaming
especially in #CyS
no one asks why the systems are so badly designed and worse implemented forget about tested
any of the bait shall be filtered in the first place,
and nothing should happen when clicked
above all the need to know principle still exercised by many in #CyS keeps the good people in the dark and the dark people in front
who actually knows what happened at JLR no one, it's kept internal 🤪
So give them their well deserved salary increase already.
"there are no exploits!"
"I see 3 walking around"
And that's why we're introducing a weaker link with agentic AI tools
Nix, I have a couple legit questions.
Do you know this guy? (Don't have to answer)
How many of the guys had Linux?
Would it made a difference if they had Linux.
Just things to sate my curiosity
@nixCraft