I've written a post on the #Capita ransomware breach, which potentially has national security implications in the UK.
- Includes technical steps orgs can take to protect themselves from a similar situation
- A call to arms on a change in how organisations handle ransomware incidents, makes case for transparency
It's a month since Russian hackers first got into #Capita, on March 22nd.
Black Basta also list Capita as CAPITA_2, just noticed - two listings.
Really interesting piece in The Times, where Capita claim that they informed clients they were hacked at 11am on Friday 31st March (the first day) and kept them briefed.
Anybody agree or disagree this was true? https://www.thetimes.co.uk/article/silence-is-deafening-after-cyberattack-on-capita-dgns935gz
Silence is deafening after cyberattack on Capita
Error messages flashed up as staff at Capita tried to log into their accounts on Friday, March 31. Frustrated workers were advised not to submit password reset requests to swamped technology teams as the outsourcer got to grips with what was going on. In a preliminary statement that morning, dictat
BBC report on the Pension Regulator concerns about the data breach at #Capita.
Capita administer pensions for around 4 million people. https://www.bbc.co.uk/news/business-65443841
#Capita were still listed unindexed on Black Basta's portal, so I entered a chat and asked Black Basta if they hacked Capita.
Black Basta erased the chat history, and removed CAPITA and CAPITA_2 from their portal just now. Previously, Capita declined to comment about communicating with Black Basta to @BleepingComputer
The Sunday Times newspaper has a big feature about ransomware today, featuring me, @ciaranmartin, @brett
I just want to call out this bit about Capita and say their failure to acknowledge the fact they lost security vetting data impacts real people, at a scale way bigger than one person - I think it is ethically poor that Capita just deny stuff that matters.
https://www.thetimes.co.uk/article/how-hackers-are-recruiting-on-the-dark-web-mpl2hvsss
However, the company could use the cyber attack to its advantage, he added.
“If Capita is smart it’ll come out of this saying we’ve more experience of handling this than anybody else, you should be using us, because we know what we’re doing and we employ leading experts in this field,” Rawlinson said.
Lmao, that’s one take.
https://www.ft.com/content/20aa4844-2ebe-44dc-9550-7d950150e784
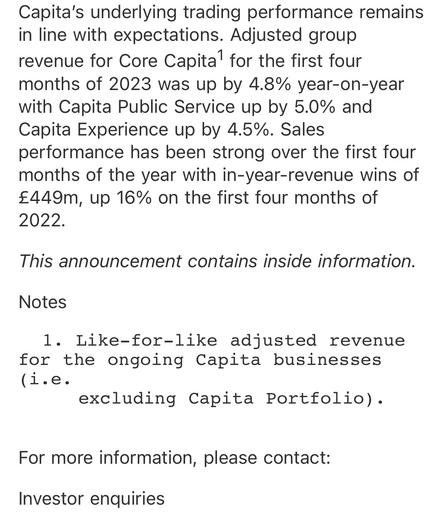
Important information about Capita’s cyber incident
Capita recently reported a cyber incident involving hackers targeting some of its computer servers – potentially impacting several of the cross-sector businesses it serves. We use Capita’s technology platform (Hartlink) to support our in-house pension administration processes and have been liaising closely with the company over the course of its forensic investigations.
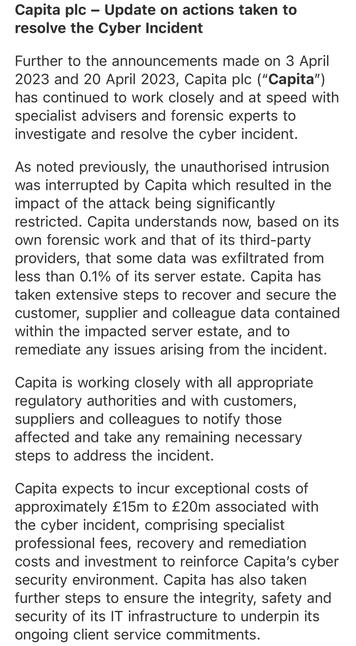
One month ago Capita’s CEO claimed their response to the attack would “go down as a case history for how to deal with a sophisticated cyber attack” - while denying any data exfiltration, and blaming the incident on a single staff member clicking a link (that bit was behind a Times paywall).
I suspect Capita’s board should be asking if somebody opening a file is the real cause of the issue - or if it’s a cascading failure to manage properly and transparently from the top down.
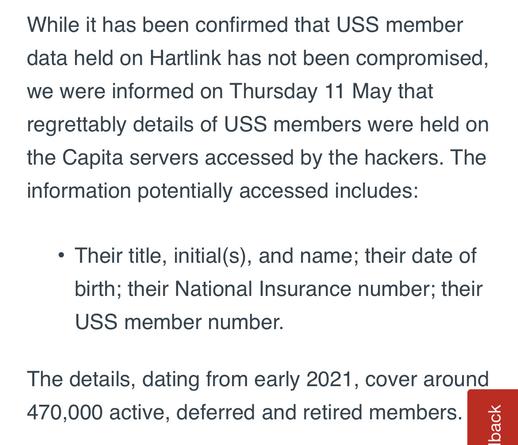
USS have today started notifying just under half a million people that #Capita lost their data to Black Basta. USS didn’t include nation insurance numbers taken.. which enables fraud.
Due to legal requirements in the UK, every pension holder in every impacted pension scheme will need to be notified individually - according to media reports, this is up to 350 pension schemes. So this may become the biggest data breach disclosure ever in the UK.
Colchester City Council has been informed they have a data breach by #Capita. Capita are telling them the data has now been “secured”. Colchester City Council say they have “extreme disappointment with Capita”. https://www.colchester.gov.uk/info/cbc-article/?id=KA-04376
Update: it turns out this was related to the S3 bucket incident.
Btw, if anybody wonders if I’m human and feel sorry for the Capita cybersecurity staff dealing with this - absolutely. I feel awful for them. I’ve always said the technical containment and investigation sounds good.
I suspect there have been people there tearing their hair out. I doubt the decisions to pretend leaked data was public domain, not admit ransomware, say 0.1% of server estate etc came from the immediate responding teams.
Diageo pension fund says their data has been compromised in #Capita breach.
“During the course of April, Capita informed us that they had taken steps to isolate and contain the incident whilst they continued to investigate it. However, on 3 May, Capita told us that it is likely a file containing your data had been compromised.”
Lots of new details in Times piece about the cybersecurity woes engulfing Capita. Features my Mastodon thread about the files on #Capita’s own website.
New victims include staff at PWC, Unilever and The Cabinet Office. 11 councils are also investigating the open bucket issue.
https://www.thetimes.co.uk/article/0513205a-f718-11ed-a712-8f47f8e830cf?shareToken=e595f233220e2a4532500771d0175ea9
Non-paywall version if you hit it: https://archive.ph/2023.05.20-234130/https://www.thetimes.co.uk/article/capita-under-fire-after-confidential-files-published-online-7cjh2jj59
If you’re wondering why specifically pension companies are disclosing, the Pension Regulator has reminded both them and Capita that there are clear and enforceable legal obligations for pensions.
The #Capita breach involves other data, including UK gov data, which has not been disclosed.
Simon Briggs (@[email protected])
Attached: 2 images Email just received from #USS about #Capita data breach. Fyi @[email protected]
Several months later, #Capita have told teachers in Sheffield they may have had a “potential” data breach. https://www.thestar.co.uk/taxonomy/term/2438/taxonomy/term/164/warning-as-sheffield-schools-hit-by-data-leak-after-hackers-target-capita-4177037
Long time readers of this very thread may remember I pointed out the Sheffield teacher breach over 2 months ago. https://doublepulsar.com/black-basta-ransomware-group-extorts-capita-with-stolen-customer-data-capita-fumble-response-9c3ca6c3b283
Remember the #Capita Black Basta ransomware incident from March? It’s still playing out months later - one of the orgs say “We remain concerned at the level of information provided to USS by Capita”
https://www.ucu.org.uk/article/13020/Update-on-USS-Capita-data-breach
Four months in, Capita have finally admitted to its own staff that their data was taken.
Auditors PWC are amongst the many other victims. They say Capita have been unable to provide “final, complete and accurate” information.
In other news, Capita and PWC have just won the contract to provide the UK’s cyber incident reporting platform. https://www.ft.com/content/52130b83-6ad7-474c-aaf7-88a549dc85e3
In #Capita’s financial results they say “minimal impact from cyber incident”, in a call with investors they described it as a non-event.
Good luck to Capita’s clients. 🫡
Just over 2000 people are taking legal action against #Capita, including some of its own employees.
Note this report contains factual inaccuracies as it relies on Capita’s version of events.
https://www.theregister.com/2023/09/13/capita_class_action_2000_claimants/
4000% increase in pension scheme breaches reported to the ICO in the UK this year.
Capita never disclosed the number of pension schemes impacted their end but I’ve heard it was… a lot.
https://www.pensionsage.com/pa/UK-pension-schemes-record-4000-pc-rise-in-cyber-security-breaches.php
Just over 5k people are suing Capita at the High Court over their ransomware data breach. Discovery on this one should be incredible.
It’s been almost a year since the #Capita ransomware incident began. Here’s how the new CEO describes it in their yearly update.
There’s now some careful rewording around data exfiltration and “recovery activities” of said data.
The exact amount they book for incident response and recovery is £25.3m, and they do not mention if insurance will cover. Overall the business has booked a £106.6m loss for the year.
This thread is almost 1000 days old and getting a resurrection. #Capita have been fined £14m by the ICO over their ransomware incident.
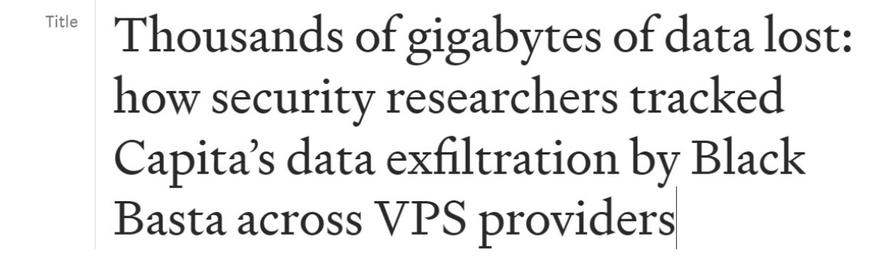
Lots of big details in the fine, including over 1tb of data stolen (as detailed in this Mastodon thread at the time), confirmation of Qakbot and my blog etc.
Their SOC was wildly understaffed. It took attacker 4 hours to get domain admin due to poor security practices. Lots of learnings for large orgs.
Capita had the PII of 6 million people exfiltrated.. but aren’t exactly sure how many still.
Additionally, they already had a major security incident running and external IR in before the encryption - while this incident was running, the attacker stole a terabyte of data over several days. The cause? No containment. They didn’t contain when they knew the attacker was on the network.
Capita had written down that it responds to all P2 alerts in its SOC with 45 minutes. It actually took them several days to reach the initial alert. They were never reaching their internal SLA.
They argued with the ICO that it is not able to regulate its internal SLAs and its regulatory overreach.. the ICO took a different view.
I wrote up my thoughts on what orgs can learn from the Capita ICO fine for their ransomware incident:
@GossiTheDog er. That's a *lot*.
Iirc CVV/CVCs are not to be stored by anyone except card issuer once the transaction is done, so that's possibly also going to be headache land for them
https://blog.pcisecuritystandards.org/faq-can-cvc-be-stored-for-card-on-file-or-recurring-transactions
@GossiTheDog Oh, well at least it wasn't anything sensitive like your
• Address;
• International address;
• Email address;
• Phone number;
• Date of birth;
• Child data;
• National Insurance (“NI”) number;
• Driver's licence / driver's licence scan;
• Passport number / passport scan;
• Photo ID scan;
• Other national ID / numbers;
• Bank account numbers and sort codes;
• Personal International Bank Account Number ("IBAN");
• Credit card number / credit card scan;
• Debit card number and CVV / debit card scan;
• Biometrics;
• Employee login details;
• Copies of signatures.
• Health information;
• Medical numbers;
• Racial/ethnic origin;
• Political beliefs;
• Religious/philosophical beliefs;
• Trade union membership;
• Sexual orientation;
• Criminal records ("CRB") checks.
@GossiTheDog I fucking hate these modern "KYC" (Know Your Customer) setups. They collect every possible piece of data about you, for what? It's not like law enforcement needs more than 1 of these to track you down. In all likelihood, the only thing this does is decrease the premiums on their fraud insurance.
Which is ironic, because if they have any *cyber* insurance, those premiums are now going to be WAY up!
@GossiTheDog I scrolled up in this thread and it's not even the first time Capita's stock has been down 18% in a day...
Kevin Beaumont (@[email protected])
Capita's share price is down 18% today. Or as Capita call it, 0.1% effected by a Happy Little Non-Event.
@GossiTheDog That reads like a Friday cryptic clue.
I think it might be CURFEW but I can't justify the UR, nor does it really mean "finished"













 🇺🇦
🇺🇦