I had forgot how big Capita are. It's like 492304932 different business units. Shodan Safari is like looking into the sun.
It looks like some of the plc centrally use Okta for authentication.. I hope they enabled Number Verification.
Capita hit by IT breakdown amid fears of cyberattack
Capita, one of the UK’s biggest outsourcers, is investigating an incident with its IT systems which has prevented staff from logging in.Employees at the company, which handles important government contracts including for the NHS, have been denied access since before 7am.They have been told in round robin phone messages “not to attempt access via VPN or submit password recovery requests”.
The Times reporter is being verbally briefed as #Capita still don't have email (almost 10 hours in).
They're told: 'There appears to be no risk to personal data processed by the business. The outage seems to be is hitting Office365 programmes including Outlook, Excel and Teams rather than client systems...'
Financial Times have a new article up about #Capita, saying two people familiar with the matter say cyber incident cannot be ruled out.
Curiously all the media articles about it this evening talk about the IT incident in the past tense - but it is still ongoing, it hasn't been resolved.
https://www.ft.com/content/00f9591f-e07a-4339-ba3e-413818602515
Verbal update from #Capita - they’re still restoring internal service, “there is no evidence that any data has been compromised."
They won’t discuss what is happening.
The Times have a report up saying #Capita NHS services staff are working using WhatsApp and Google Drive, rather than approved Microsoft tooling.
Massively concerned by lack of transparency, going to start digging into this tomorrow with officials. https://www.thetimes.co.uk/article/capita-dogged-by-it-problem-for-three-days-wthl2zp5v
#Capita are listed on Black Basta ransomware portal as a victim.
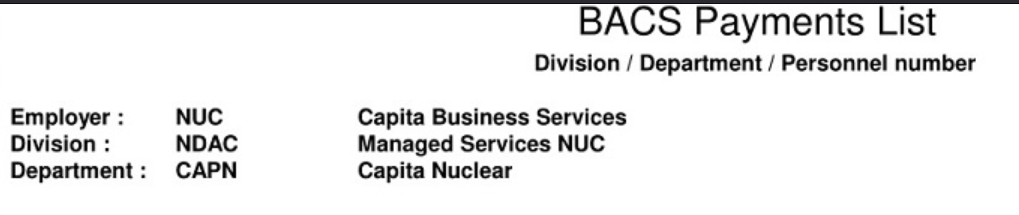
They posted various screenshots of access to personal data (e.g. passport scans), security vetting, nuclear BACS payment details, architecture diagrams, school reports etc - Capita customer data.
http://stniiomyjliimcgkvdszvgen3eaaoz55hreqqx6o77yvmpwt7gklffqd.onion/?id=CAPITA
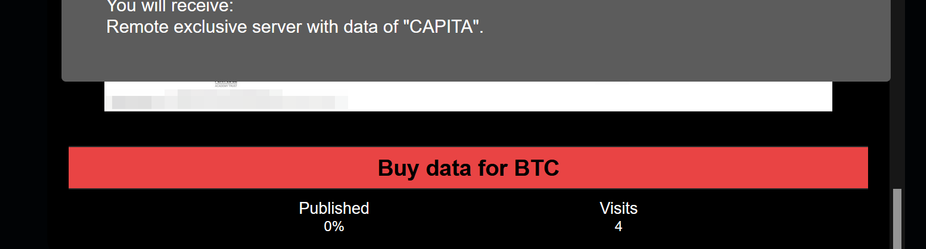
#Capita's breach is also being sold on the portal, you can pay cryptocurrency for "Remote exclusive server with data of "CAPITA""
Black Basta focus on data exfiltration, traditionally using rclone. Prior reading: https://www.hhs.gov/sites/default/files/black-basta-threat-profile.pdf
I took a look at Capita’s ransomware incident, and look at what they’ve told the media and customers versus the reality of what has happened.
Black Basta ransomware group extorts Capita with stolen customer data, Capita fumble response.
Black Basta ransomware group extorts Capita with stolen customer data, Capita fumble response.
There’s an interesting piece in The Times today, where the CEO of Capita declares Capita’s response to the hack “will go down as a case history for how to deal with a sophisticated cyberattack”…
The Times website has a report this evening about the Black Basta breach of Capita. Capita still deny there is any evidence of data being compromised.. in a story that even includes details of Capita’s office floor plans leaking. #ransomware
The Record reports #Capita is "...understood to be working to establish whether the data is authentic or if the extortion group had cobbled it together from other sources."
Maybe the source is cobbled together from Capita Business Services... or Capita Nuclear. Or one of the other Capita business units in the #BlackBasta portal. https://therecord.media/capita-investigates-authenticity-data-leak
After two weeks of telling press and customers privately my blog was inaccurate, suggesting the leaked data was public domain, denying it was ransomware etc.. #Capita have now admitted a data breach.
They’re still not giving full story or admitting Black Basta, more to come on how to defend your org.
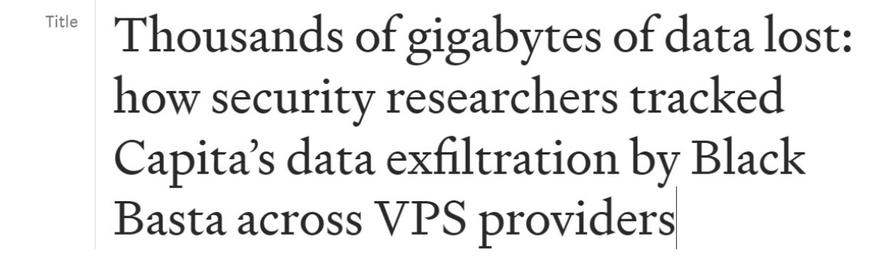
I've written a post on the #Capita ransomware breach, which potentially has national security implications in the UK.
- Includes technical steps orgs can take to protect themselves from a similar situation
- A call to arms on a change in how organisations handle ransomware incidents, makes case for transparency
It's a month since Russian hackers first got into #Capita, on March 22nd.
Black Basta also list Capita as CAPITA_2, just noticed - two listings.
Really interesting piece in The Times, where Capita claim that they informed clients they were hacked at 11am on Friday 31st March (the first day) and kept them briefed.
Anybody agree or disagree this was true? https://www.thetimes.co.uk/article/silence-is-deafening-after-cyberattack-on-capita-dgns935gz
Silence is deafening after cyberattack on Capita
Error messages flashed up as staff at Capita tried to log into their accounts on Friday, March 31. Frustrated workers were advised not to submit password reset requests to swamped technology teams as the outsourcer got to grips with what was going on. In a preliminary statement that morning, dictat
BBC report on the Pension Regulator concerns about the data breach at #Capita.
Capita administer pensions for around 4 million people. https://www.bbc.co.uk/news/business-65443841
#Capita were still listed unindexed on Black Basta's portal, so I entered a chat and asked Black Basta if they hacked Capita.
Black Basta erased the chat history, and removed CAPITA and CAPITA_2 from their portal just now. Previously, Capita declined to comment about communicating with Black Basta to @BleepingComputer
The Sunday Times newspaper has a big feature about ransomware today, featuring me, @ciaranmartin, @brett
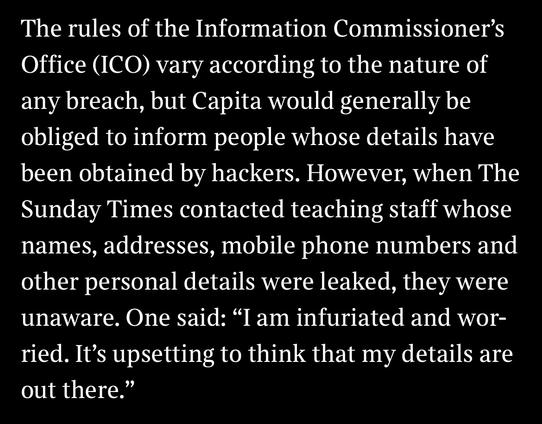
I just want to call out this bit about Capita and say their failure to acknowledge the fact they lost security vetting data impacts real people, at a scale way bigger than one person - I think it is ethically poor that Capita just deny stuff that matters.
https://www.thetimes.co.uk/article/how-hackers-are-recruiting-on-the-dark-web-mpl2hvsss
However, the company could use the cyber attack to its advantage, he added.
“If Capita is smart it’ll come out of this saying we’ve more experience of handling this than anybody else, you should be using us, because we know what we’re doing and we employ leading experts in this field,” Rawlinson said.
Lmao, that’s one take.
https://www.ft.com/content/20aa4844-2ebe-44dc-9550-7d950150e784
Important information about Capita’s cyber incident
Capita recently reported a cyber incident involving hackers targeting some of its computer servers – potentially impacting several of the cross-sector businesses it serves. We use Capita’s technology platform (Hartlink) to support our in-house pension administration processes and have been liaising closely with the company over the course of its forensic investigations.
One month ago Capita’s CEO claimed their response to the attack would “go down as a case history for how to deal with a sophisticated cyber attack” - while denying any data exfiltration, and blaming the incident on a single staff member clicking a link (that bit was behind a Times paywall).
I suspect Capita’s board should be asking if somebody opening a file is the real cause of the issue - or if it’s a cascading failure to manage properly and transparently from the top down.
USS have today started notifying just under half a million people that #Capita lost their data to Black Basta. USS didn’t include nation insurance numbers taken.. which enables fraud.
Due to legal requirements in the UK, every pension holder in every impacted pension scheme will need to be notified individually - according to media reports, this is up to 350 pension schemes. So this may become the biggest data breach disclosure ever in the UK.
Colchester City Council has been informed they have a data breach by #Capita. Capita are telling them the data has now been “secured”. Colchester City Council say they have “extreme disappointment with Capita”. https://www.colchester.gov.uk/info/cbc-article/?id=KA-04376
Update: it turns out this was related to the S3 bucket incident.
Btw, if anybody wonders if I’m human and feel sorry for the Capita cybersecurity staff dealing with this - absolutely. I feel awful for them. I’ve always said the technical containment and investigation sounds good.
I suspect there have been people there tearing their hair out. I doubt the decisions to pretend leaked data was public domain, not admit ransomware, say 0.1% of server estate etc came from the immediate responding teams.
Diageo pension fund says their data has been compromised in #Capita breach.
“During the course of April, Capita informed us that they had taken steps to isolate and contain the incident whilst they continued to investigate it. However, on 3 May, Capita told us that it is likely a file containing your data had been compromised.”
Lots of new details in Times piece about the cybersecurity woes engulfing Capita. Features my Mastodon thread about the files on #Capita’s own website.
New victims include staff at PWC, Unilever and The Cabinet Office. 11 councils are also investigating the open bucket issue.
https://www.thetimes.co.uk/article/0513205a-f718-11ed-a712-8f47f8e830cf?shareToken=e595f233220e2a4532500771d0175ea9
Non-paywall version if you hit it: https://archive.ph/2023.05.20-234130/https://www.thetimes.co.uk/article/capita-under-fire-after-confidential-files-published-online-7cjh2jj59
If you’re wondering why specifically pension companies are disclosing, the Pension Regulator has reminded both them and Capita that there are clear and enforceable legal obligations for pensions.
The #Capita breach involves other data, including UK gov data, which has not been disclosed.
Simon Briggs (@[email protected])
Attached: 2 images Email just received from #USS about #Capita data breach. Fyi @[email protected]
Several months later, #Capita have told teachers in Sheffield they may have had a “potential” data breach. https://www.thestar.co.uk/taxonomy/term/2438/taxonomy/term/164/warning-as-sheffield-schools-hit-by-data-leak-after-hackers-target-capita-4177037
Long time readers of this very thread may remember I pointed out the Sheffield teacher breach over 2 months ago. https://doublepulsar.com/black-basta-ransomware-group-extorts-capita-with-stolen-customer-data-capita-fumble-response-9c3ca6c3b283
Remember the #Capita Black Basta ransomware incident from March? It’s still playing out months later - one of the orgs say “We remain concerned at the level of information provided to USS by Capita”
https://www.ucu.org.uk/article/13020/Update-on-USS-Capita-data-breach
@GossiTheDog Are you sure it's only two deceased patients?
The wording on the statement you linked to mentions "two files containing names and NHS numbers of deceased & de-registered patients", which sounds to me like it could contain more than two deceased patients, and may even contain data about people who are still alive.
@GossiTheDog I keep checking Capita's news page to see whether they've started doing daily updates.
"Today we informed our client X that Y# customer records were stolen during incident [1/2], consisting of personal information A, B, C, D and E."
Not today though. Maybe tomorrow... 😕
The ICO could also do better. Disappointing approach by lots of different entities & people.
"The information accessed includes your title, initial(s), and name, your date of birth, your National Insurance number, your USS member number and your retirement date"
@GossiTheDog
I'm thinking about how this could've been spotted sooner.
It's probably not realistic to rely purely on end-user training. So perhaps this should be a feature of data protection systems:
"This email contains a link to a file which is accessible to the general public. This may be a GDPR breach, or a sign of insecure file storage. This has been flagged with the company DPO."
Or unauthenticated download links could just be blocked.
Is this a feature of any email systems already?
Perhaps it's finally time to insource rather than outsource 🤔


 🇪🇺🏳️🌈
🇪🇺🏳️🌈