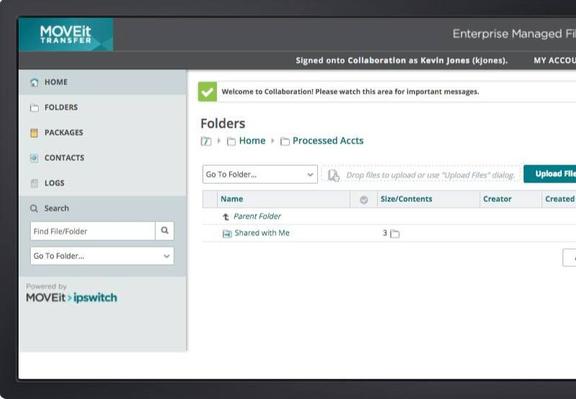
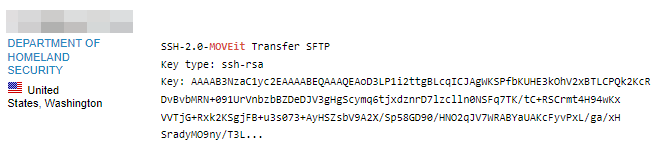
A bunch of people have alerted me to a vulnerability in #MoveIT, a secure file transfer app used heavily in the UK.
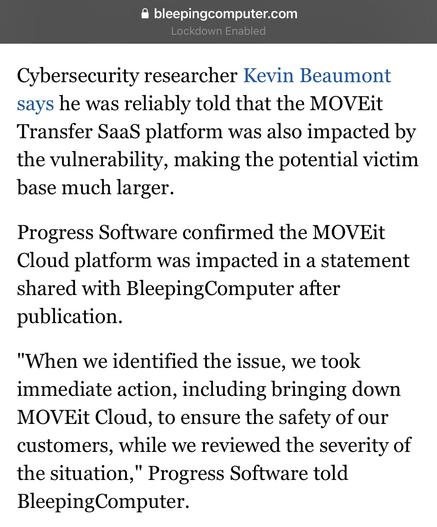
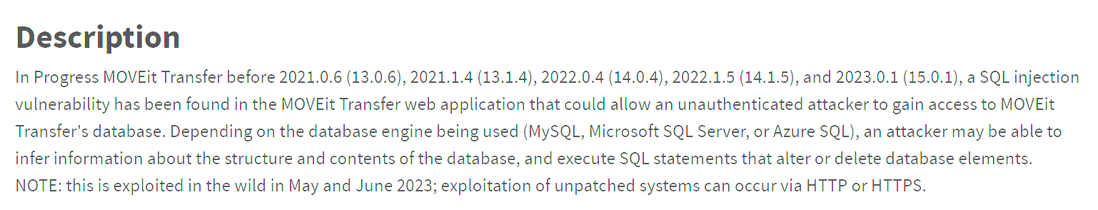
I did some digging and it looks like it’s a zero day under active exploitation. Not 100% on threat actor yet but it may be one of the ransomware/extortion groups.
Really serious, impacted orgs should shut down the server. Thread follows. #threatintel