With #MoveIT Transfer, stuff I know so far:
- Huge US footprint, including US government. It's quite expensive, so mostly western enterprises.
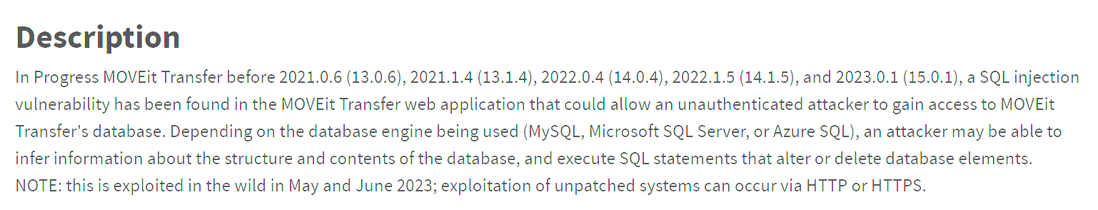
- It's definitely a zero day, although vendor doesn't want to say it obvs.
- Every one online is still vulnerable. This includes some big banks etc.
- Webshells started being planted a few weeks ago, multiple incidents running at multiple orgs during that timeframe who detected activity.
Vendor appears pretty responsive and good so far.
More info about one of the #MoveIT webshells in this write up
YARA rule for that webshell https://github.com/AhmetPayaslioglu/YaraRules/blob/main/MOVEit_Transfer_Critical_Vulnerability.yara
Example file (0 AV detection still) https://www.virustotal.com/gui/file/387cee566aedbafa8c114ed1c6b98d8b9b65e9f178cf2f6ae2f5ac441082747a/summary
Just been on a quick call with industry peeps looking at what known attacker IPs were interacting with over the weekend - #MoveIT boxes in the US and SaaS.
It vuln itself allows RCE, not just webshells, so I think Mandiant and DART are gonna get some IR hours.
While I’m here - make sure MoveIT Transport is in a real DMZ. Your shit would still have been stolen but it stops them moving internally.
It looks like a significant amount of data exfiltration may have happened re #MoveIT. Another problem - it can use cloud bucket storage for data, and storage access keys got taken and need rotating: data access still possible in those situations.
There are conflicting signals re exploitation - while it’s clear a smash and grab happened at weekend, there’s signs exploit was used prior to weekend.
#MoveIT Transport zero day issue has a CVE now under review - CVE-2023-34362.
HT @CyberLeech #CVE202334362
Microsoft are attributing the #moveIT zero day attacks to cl0p ransomware group.
I’ve been tracking this - there are a double digit number of orgs who had data stolen, that includes multiple US Government and banking orgs.
This is the third time Cl0p ransomware group have used a zero day in webapps for extortion in three years, btw. In all three cases they were products with security in the branding.
In terms of emerging threats, expect more of this while the west appears unable to accept the threat of ransomware groups.
#moveIT issue is unfolding fast.
British Airways and Boots (retailer) in UK have disclosed they had data breaches via moveIT. https://news.sky.com/story/bas-uk-staff-exposed-to-global-data-theft-spree-12896900
Just to be crystal clear on this one - orgs running #MoveIT Transfer should assume compromise, not just patch.
Cl0p did a smash and grab over the last holiday weekend across over a hundred large/prominent orgs.
Check for webshells. It’s not just human2, look for new files in the web root folder.
Cl0p drip feed victims on their portal over months, not days - this is the third time they’ve pulled a zero day heist like this.
Somebody asked me an interesting question earlier regarding #moveIT - why aren't US orgs disclosing breaches?
Really simple - they don't have to due to lack of data protection law, or they're trying to cover it up via payment to cl0p.
A majority of the victims, from scanning, are in the US - Europe is actually a small minority.
EY - auditor Ernst & Young - have started informing clients of data breach with #moveIT. I understand payroll and tax data impacted. #threatintel
(Tooting this again as I accidentally deleted it, UI sucks).
Shell Oil were hit with a ransomware group breach via a zero day in Accellion MFT product in 2021, so they moved to MoveIT: https://www.zdnet.com/article/oil-giant-shell-discloses-data-breach-linked-to-accellion-fta-vulnerability/
In 2023 they’ve been hit with a zero day by a ransomware group in their MoveIT MFT: https://therecord.media/shell-impacted-in-clop-ransomware-attack
Ransomware groups are out of control.