#xmlrpc gehört zu den älteren Schnittstellen von #WordPress und stammt aus einer Zeit, in der #Webseiten noch deutlich einfacher aufgebaut waren als heute. Trotzdem spielt die Funktion bis heute eine Rolle, vor allem im Bereich #Sicherheit und #wartung
https://techygeekshome.info/how-to-check-if-your-website-or-plugins-are-using-xml-rpc/?fsp_sid=43847
https://techygeekshome.info/how-to-check-if-your-website-or-plugins-are-using-xml-rpc/?fsp_sid=38699
https://marcindudek.dev/blog/xmlrpc-brute-force-cache-rate/ #cachedetective #XMLRPC #brute-force #security #SherlockHolmes #technews #HackerNews #ngated
288,493 Requests – How I Spotted an XML-RPC Brute Force from a Weird Cache Ratio
https://marcindudek.dev/blog/xmlrpc-brute-force-cache-rate/
#HackerNews #XMLRPC #BruteForce #CacheRatio #Security #Analysis #Cybersecurity #TechInsights
https://techygeekshome.info/how-to-check-if-your-website-or-plugins-are-using-xml-rpc/?fsp_sid=22729
Ich habe mir vorgenommen, wieder häufiger zu bloggen und bin dabei direkt in ein Problem gelaufen:
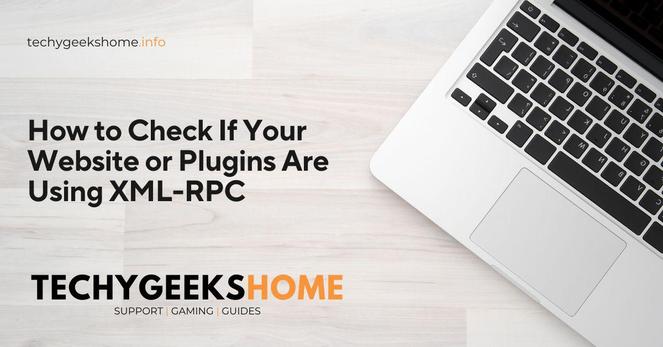
Stolperstein 2FA bei WordPress-Zugriff per XML-RPC (Wordfence)
https://schacknetz.de/stolperstein-2fa-bei-wordpress-zugriff-per-xml-rpc-wordfence/
after working months on API and architecture improvements, I've published version 0.8.0 of `dxr`, my #xmlrpc implementation for #Rust 
the public API hasn't changed *much*, but it should be nicer to use for some cases. also, internal implementation details no longer leak into the public API - I finally managed to decouple XML de/serialization from the public types 😊
release notes: https://codeberg.org/decathorpe/dxr/releases/tag/v0.8.0
phew, I'm glad this won't be banging around in my head any more.
https://techygeekshome.info/how-to-check-if-your-website-or-plugins-are-using-xml-rpc/?fsp_sid=23183
Odoo XMLRPC CRUD: Unlock 5 proven steps to master external integration and automate your Odoo data operations. #Odoo #XMLRPC #Integration #Automation #APIs
https://teguhteja.id/odoo-xmlrpc-crud-proven-steps/?utm_source=mastodon&utm_medium=jetpack_social