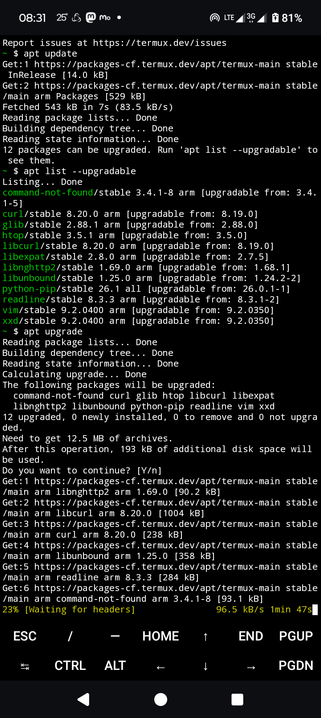
Do not forget to always patch your Linux / BSD distributions wherever they may reside.
Forgetting to do so may open up your systems for known exploits which is easily avoidable, from the InfoSec perspective
In case you don't know termux yet on ARM architecture go read and learn
Sources:
man man(1)
man apt
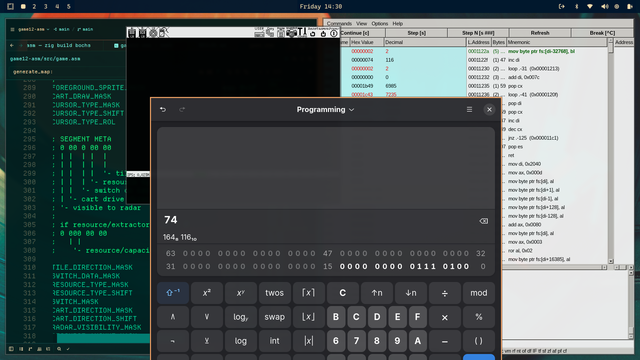
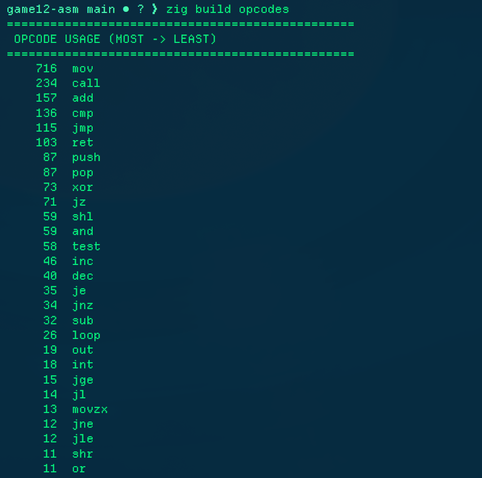
#Linux #termux #Patch #update #upgrade #programming #BSD #InfoSec #ARM #X86 #freedom #OpenSource