Getting ready for the cybersecurity certification exam — Lab 3 (API) — Apply a 100% discount on the site
Getting ready for the cybersecurity certification exam — Lab 2 (API) — Buy an item for $0
lt3ua_002_en
Mobile Application VAPT: Why Your Business Apps Need Security Testing
Learn why mobile app VAPT is essential to protect business data, prevent breaches, and ensure compliance with regular security testing.
Learn more: https://infotechecs.livepositively.com/mobile-application-vapt-why-your-business-apps-need-security-testing/
#VAPT #MobileSecurity #AppSecurity #CyberSafety #CyberSecurity #SecureYourApp #MobileAppSecurity #DataProtection #VulnerabilityTesting #ECSInfotech #ECS
Mobile App VAPT: What You Need to Know to Keep Your Apps Safe from Unknown Threats
Stay ahead of cyber threats with Mobile App VAPT. Learn how vulnerability assessment and penetration testing keep your mobile apps secure from unknown risks.
👉 Read the full blog to learn more: https://www.ecsinfotech.com/mobile-app-vapt-keep-your-apps-safe-from-unknown-threats/
#MobileAppVAPT #CyberSecurity #MobileAppSecurity #AppVulnerability #VAPT #VulnerabilityTesting #PenetrationTesting #AppProtection #DataSecurity #CyberAwareness #MobileApps #ECSInfotech #ECS
HackGPT Enterprise, developed by Yashab Alam, merges GPT-4, Ollama, and ML frameworks to automate penetration testing across multi-cloud environments.
It covers reconnaissance to reporting with CVSS risk scoring, compliance mapping, and secure architecture built on Docker + Kubernetes.
Balanced automation or a security tradeoff?
Follow TechNadu for unbiased insights into AI and cybersecurity convergence.
#CyberSecurity #AI #HackGPT #PenTesting #MachineLearning #DevSecOps #VulnerabilityTesting #EthicalHacking #Automation #TechNadu
New Open-Source Tool Spotlight 🚨🚨🚨
Nuclei is a tool for automating vulnerability scanning using customizable YAML-based templates. Its strength lies in speed and flexibility, making it ideal for penetration testers and security researchers. Think of it as crafting your own scanner that adapts to your needs. #CyberSecurity #VulnerabilityTesting
🔗 Project link on #GitHub 👉 https://github.com/projectdiscovery/nuclei
#Infosec #Cybersecurity #Software #Technology #News #CTF #Cybersecuritycareer #hacking #redteam #blueteam #purpleteam #tips #opensource #cloudsecurity
— ✨
🔐 P.S. Found this helpful? Tap Follow for more cybersecurity tips and insights! I share weekly content for professionals and people who want to get into cyber. Happy hacking 💻🏴☠️
GitHub - projectdiscovery/nuclei: Nuclei is a fast, customizable vulnerability scanner powered by the global security community and built on a simple YAML-based DSL, enabling collaboration to tackle trending vulnerabilities on the internet. It helps you find vulnerabilities in your applications, APIs, networks, DNS, and cloud configurations.
Nuclei is a fast, customizable vulnerability scanner powered by the global security community and built on a simple YAML-based DSL, enabling collaboration to tackle trending vulnerabilities on the ...
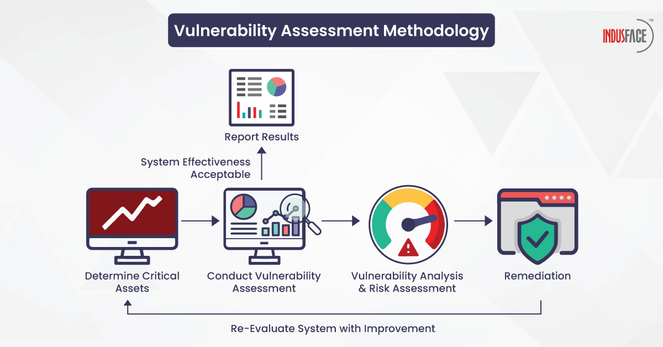
🔒 Strengthen your defenses with our foolproof #vulnerabilityassessment methodology.
Our step-by-step guide will help you build a robust defence for your business, from setting security objectives to implementing measures.
Learn more: https://bit.ly/48r9wT9
#vulnerabilities #vulnerabilityscanning #potentialthreats #pentesting #xss #owasp #apis #ddos #vulnerabilitytesting #securitymisconfiguration #webappscanning #indusfacewas