#Denuvo #Warez #Buzzheavier #FitGirlRepacks #M4CKD0GERepack #SteamUnderground #Vikingfile #VMProtect #voices38 https://sc.tarnkappe.info/61f519
#Denuvo #Warez #Buzzheavier #FitGirlRepacks #M4CKD0GERepack #SteamUnderground #Vikingfile #VMProtect #voices38 https://sc.tarnkappe.info/61f519
#Denuvo #Gaming #RedLynx #RUNE #TrialsRising #UbisoftKiew #VMProtect https://sc.tarnkappe.info/7dc474
In depth analysis of VMProtect 2 internals (2021)
Part 1: https://blog.back.engineering/17/05/2021/
Part 2: https://blog.back.engineering/21/06/2021/
VMProtect 2 - Detailed Analysis of the Virtual Machine Architecture
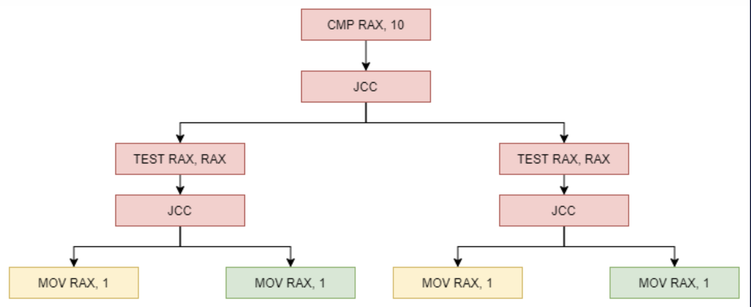
VMProtect 2 is a virtual machine based x86 obfuscator which converts x86 instructions to a RISC, stack machine, instruction set. Each protected binary has a unique set of encrypted virtual machine instructions with unique obfuscation. This project aims to disclose very significant signatures which are in every single VMProtect 2 binary with the intent to aid in further research...
Анализ виртуальной машины на примере VMProtect. Часть 2
В первой части статьи мы рассмотрели общий вид работы конвейера виртуальной машины, а также немного коснулись возможных подходов для анализа виртуальной машины. В этой части статьи не приводится гарантированного способа снятия виртуализации, я просто хочу поделиться опытом анализа ВМ который позволяет более-менее понять что-то о работе ВМ и может быть полезен при анализе схожих реализаций. Анализировать!
https://habr.com/ru/articles/835768/
#malware #vmprotect #reverseengineering #реверсинжиниринг #вредоносное_программное_обеспечение #исследование #обфускация #антиотладочные_приемы
Анализ виртуальной машины на примере VMProtect. Часть 1
В этой статье мы рассмотрим, как может выглядеть работа виртуальной машины VMProtect , а также посмотрим, что можно сделать для понимания защищенного функционала (в зависимости от того, как далеко вы готовы зайти в этом не всегда благодарном деле). Ожидается, что данный материал поможет тем, кто в ходе реагирования на компьютерный инцидент или исследования какой-либо вредоносной активности столкнулся с защитой в виде виртуальной машины. Анализировать!
https://habr.com/ru/articles/781592/
#malware #vmprotect #ida #incident_response #cybersecurity #кибербезопасность #вредоносное_программное_обеспечение #информационная_безопасность #reverseengineering
#Denuvo #Empress #Warez #CapcomAntiTamper #Crack #DenuvoSecureDLCv2 #ResidentEvil4 #VMProtect https://tarnkappe.info/artikel/empress/resident-evil-4-trotz-denuvo-version-18-gecrackt-274678.html
Oh look, more dubious drivers protected by vmprotect.
A driver protected by vmp should be an indicator of compromise at this point.
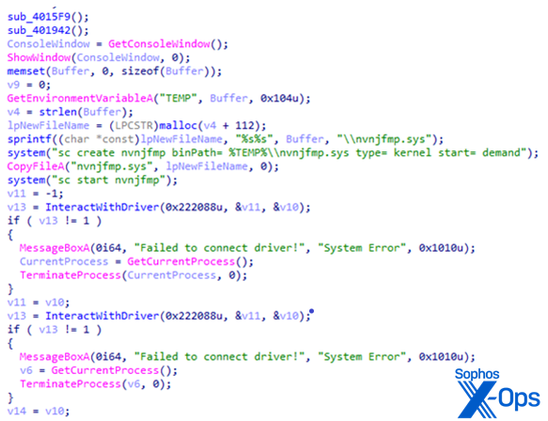
In the course of doing our research, we studied older variants of #BURNTCIGAR #drivers, and compared them to the new ones we were encountering during the incident response.
We found that these new drivers had been obfuscated with a variety of techniques, specifically that the drivers were packed using a commercial runtime #packer called #VMprotect. The packer makes it more difficult for an analyst to reverse-engineer a #malware sample, but we don't see a lot of drivers that are packed, at all. It was kind of unusual.
In addition, the malware drivers requires the threat actor to run an executable called a loader, which simply does the mechanical work of creating Services entries in the Windows Registry, and moving the driver into the %temp% directory. The loader isn't packed.
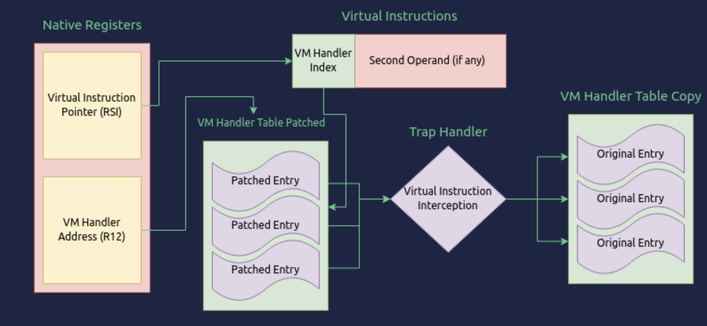
Extracting VMProtect handlers with Binary Ninja
I've started looking into the Adylkuzz malware, as mentioned by Tim Blazytko in his article on Automated Detection of Obfuscated Code. Initial analysis shows a TLS entry handler that dumps us straight into a VMProtect VMEnter() function, that looks l...