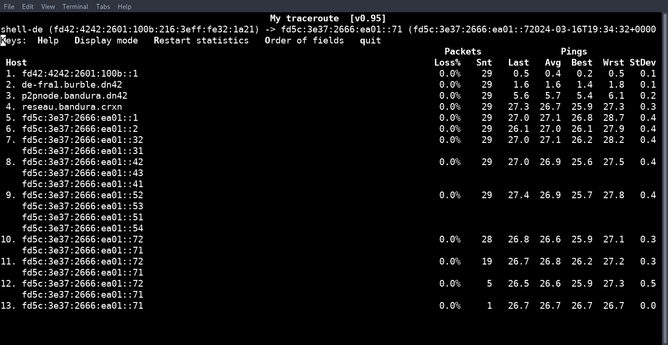
Some time ago I asked myself what happens if I have a case with traceroute where a response comes from two different addresses. I then develop crazytrace. The project is available on CodeBerg under the GPL3: https://codeberg.org/mark22k/crazytrace Today I also tried to roll out the project on reseau.mk16.de (CRXN) and it worked!
I have written my first (two-line long) patch for Ruby [1]. This should soon make my traceroute written in Ruby work everywhere without any problems [2][3]!
[1] https://github.com/ruby/ruby/pull/9930
[2] https://codeberg.org/mark22k/hoptracker
[3] https://rubygems.org/gems/hoptracker
So the #bauhaus fi website supports #IPv6 which is great! What isn't great though, is that they block path MTU, so if You're (like me) on a VPN with an MTU less than 1500 bytes You're out of luck and cannot surf bauhaus' site. This would merely be a fragmentation thing, but since there's SSL involved there are always max sized packages and I think one cannot fragment SSL-packets, can you?
Anyone with connections, the geoip tells me it's in Germany?
$ tracepath 2a02:2e0:cd4d::6
1?: [LOCALHOST] 0.029ms pmtu 1438
<clip>
5: fi-csc.nordu.net 7.838ms
6: se-tug.nordu.net 18.861ms asymm 8
7: netnod-ix-ge-a-sth-1500.core-backbone.com 19.258ms asymm 9
8: 2a01:4a0:1338:114::2 20.017ms asymm 10
9: 2a02:2e0:cd4d::6 18.744ms !A
Resume: pmtu 1438
Note the !A result of #tracepath
English: https://mk16.de/blog/traceroute-and-tracepath/
German: https://mk16.de/blog/traceroute-und-tracepath/
#traceroute #tracepath #networking #routing #tools #linux #ping
origin_net 2001:db8:9::/64
server_net 404:200:386::/56
opn.haj.net AAAA 404:200:386:d::301
pl.haj.net AAAA 404:200:386:f:1:2:3:c
s3.haj.net AAAA 404:200:386:d::450
hop hop_address
1. 2001:db8:9::1 [router (CPE)]
2. 2001:db8:79::f4 [ISP]
[...] [IP transit, many ASes]
9. 404:100:1::1 [ISP]
10. 404:100:386::200 [router (CPE)]
11. 404:100:386:d::301 [bare metal/vm/container]
12. 404:100:386:f:1:2:3:c [vm/container]
Let's say that you know that exists a service with name "pl.haj.net" and then want to scan it, but isn't enough and I want more hosts from that network.
By common knowledge, you know that's 99% certainly that network is at least /64, so you can start to do "lateral scan" and try common addresses based in the prefix of "pl.haj.net" or random address. Common address e.g. ::1 ~ ::f, ::cafe, ::deef, ::dead, ::1337.
Also, how is a e2e communication, you know that the previous hops are routers, L3 switches or some kind of device that can do IPv6 forwarding (hops 10 and 11), so it's worth to try scan them too since you already have their address from a traceroute.
Now you have a hint that network is possible to be at least a /60 prefix, so you can now try a new lateral scan at 404:100:386:0::/60 using ::1 and ::2 as suffix to guess new or same hosts. Then you have (16^1)*2 possibilities for /60 and (16^2)*2 for /56 where suffix is ::1 and ::2.
Still many address to try but they have a nice probability to guess right instead of random address.
Another method is to search prefixes that have at least one AAAA record (not PTR) like this: https://bgp.he.net/net/2001:67c:1be8::/48#_dns
You have many AAAA records with same address within a /48 and now you know more domains that you can follow links to try find new DNS records of that domain.
That's why you shall apply firewall rules at your border router and accept certain destination ports/protocols and allow access to management services from a address list.
About ICMPv6¹, you shall allow only type 1 and 2+code 0 [Packet too big] from WAN to not break PMTUD. Or more simple, drop packets with ICMPv6 type 3 that go to WAN (output and forward), so this helps to hide middle hops and will show only the last one.
¹ https://www.iana.org/assignments/icmpv6-parameters/icmpv6-parameters.xhtml
#ipv6 #icmpv6 #mtr #traceroute #tracepath