jemand verwendet noch #Suse ?🫣
[$] LLM-driven security reports disrupt coordinated disclosure
Predictions that LLM tools would cause a surge in reports of security vulnerabilities have, unquestionably, borne out. As expected, maintainers are having to wade through more secu [...]
https://lwn.net/Articles/1070698/ #LWN #Linux #security #Debian #SUSE #RedHat #Gentoo #Python #Git
Im April fand die #SUSECON statt - über 1.000 Teilnehmende haben sich auf den Weg nach Prag gemacht um aus den 140 Sessions auszuwählen. Neben dem aktuellen Trendthema #DigitalSovereignty gab es auch zahlreiche technische Neuigkeiten rund um #SUSE #Linux Enterprise, SUSE Linux Micro und Multi-Linux Manager. Neben einem Event-Wrap-Up mit Maximilian Herrmann haben wir auch Interviews mit Stefan Behlert, Johannes Hahn und Miguel Pérez Colino für euch.

E019 - SUSECON 2026
#SUSECON26 Im April fand die SUSECON statt - über 1.000 Teilnehmende (und wir) haben sich auf den Weg nach Prag gemacht um aus den 140 angebotenen Sessions auszuwählen. Neben dem aktuellen Trendthema "Digital Sovereignty" gab es auch zahlreiche technische Neuigkeiten rund um SUSE Linux Enterprise, SUSE Linux Micro und Multi-Linux Manager. Neben einem Event-Wrap-Up mit Maximilian Herrmann (IT-Berater) haben wir auch zwei Interviews mit Stefan Behlert (Product Manager, SUSE) und Johannes Hahn (Engineering Director, SUSE) sowie Miguel Pérez Colino (General Manager Linux Business Unit, SUSE) für euch.
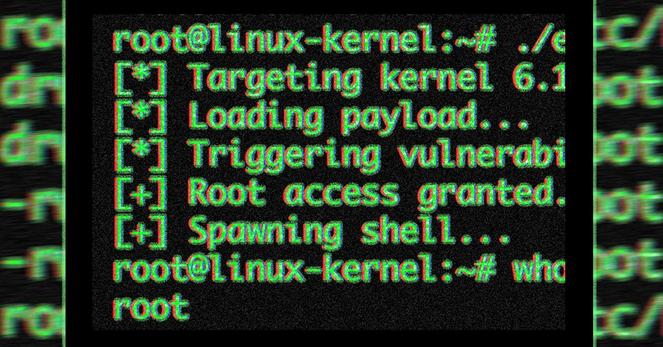
Lien recensant l'ensemble des #correctifs pour les #distributions #Linux contre #CopyFail :
https://mstdn.social/@jschauma/116505274281284939
#CopyFail #Patch #Update #Vulnerability #Security #Cybersecurity #Ubuntu #Debian #Fedora #Suse #RedHat #Alpine #AlmaLinux #Trixie #Root #Kernel #Docker #Kubernetes #PrivilegeEscalation #Privilege #UserPrivilege
« Mettez à jour le paquet du noyau de votre distribution avec une version incluant le #commit a664bf3d603d de la branche principale », expliquent les chercheurs, « la plupart des principales distributions proposent désormais ce correctif », comme #Debian (https://security-tracker.debian.org/tracker/CVE-2026-31431) (Forky et Sid), #Ubuntu (https://ubuntu.com/security/CVE-2026-31431), par exemple mais la mise en place est encore en cours chez #RedHat (https://access.redhat.com/security/cve/cve-2026-31431) et #Suse.
Fin de l'article.
10/
#Patch #Linux #Ubuntu #CopyFail #Root #Cybersecurity #Docker #Kubernetes
Feed: All Latest | Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers by Dan Goodin, Ars Technica
AI generated summary, Read the full article for complete information.
A newly disclosed Linux kernel vulnerability, dubbed CopyFail (CVE‑2026‑31431), enables a local privilege‑escalation that lets an unprivileged attacker obtain root on virtually any Linux distribution with a single, unmodified script. Released by security firm Theori after a brief private disclosure, the flaw resides in the kernel’s crypto API where an AEAD template copy operation overwrites adjacent memory, allowing the attacker to elevate privileges, break out of containers, compromise multi‑tenant systems, and hijack CI/CD pipelines. Although patches were quickly issued for several kernel versions (7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254), many distributions had not yet applied them, leaving countless desktops, servers, and cloud environments exposed. Experts warn that the exploit’s reliability surpasses earlier high‑profile kernel bugs like Dirty Pipe and Dirty Cow, and they urge all Linux users to verify that their systems incorporate the relevant fixes or follow vendor mitigation guidance.
#Theori #Ubuntu #Amazon #SUSE #Debian #RedHat #Fedora #ArchLinux #Kubernetes #Linux #copyfail #security #security_cyberattacksandhacks #security_securitynews
Copy Fail (CVE-2026-31431), disclosed Wednesday by security firm Theori, lets any local #Linux user gain root access on #Ubuntu, Amazon Linux, #RHEL, and #SUSE. The bug traces to a 2017 optimization in the kernel’s AEAD crypto path; an #AI powered scanner reportedly found it after just one hour of analysis. Kernel patches are available and SUSE called the flaw “extremely dangerous,” urging administrators to update or blacklist the algif_aead module immediately.

Copy Fail: 732 Bytes to Root on Every Major Linux Distribution. - Xint
Xint Code disclosed CVE-2026-31431, an authencesn scratch-write bug chaining AF_ALG + splice() into a 4-byte page cache write. A 732-byte PoC gets root on Ubuntu, Amazon Linux, RHEL, SUSE. | AI for Security, Vulnerability Research



 🚩🏴
🚩🏴