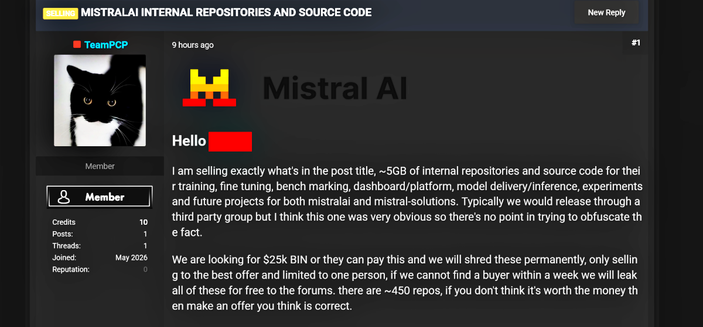
TeamPCP hackers target Mistral AI code repos for sale
Hackers from TeamPCP are demanding $25,000 for nearly 5 gigabytes of stolen Mistral AI code, threatening to leak it for free if they don't find a buyer within a week. The group claims to have snagged around 450 internal repositories, including sensitive source code used for training and model delivery.
#Teampcp #Ransomware #EmergingThreats #MistralAi #CodeRepositories