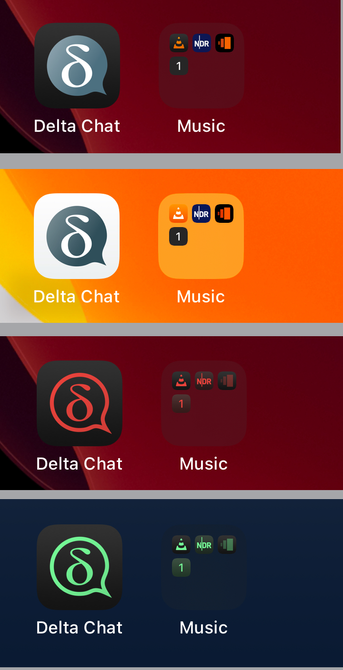
"How U2F (2FA) works at Twitter" - Part 2/2 of a #tootSeries about #ITsecurity #MultiFactor #insights. [Ref. "MOMOC-04-Comfort/Security"]
#MOMOCtips
#Smartphones and #USBkeys that support #NFC (Near-Field Communication), like for example the #Yubikey NEO, lets you log in with U2F without needing a physical cable to insert the USB key. Put it close to the phone (back side), and the #authentication happens over the air. Unlike other solutions (like the #Nitrokey which only support 1 function), having a Yubikey which normally supports 2 functions, you can have BOTH the static password AND the U2F on the same key working through NFC wirelessly. A long-press on the button emits the stored static password to the phone clipboard so that you can paste it into the password field, and then second factor (U2F) function asks you to confirm by pressing the button briefly, and then you are logged in.
PS. NEVER use a static password in the exact form it is stored! If someone steals or finds your #USBkey, you do not want them to be able to use it by itself. A #trick is to never use it exactly as it is stored on the key:
- Remove a few characters after it has been pasted/sent to the password field, and then ADD some characters manually which are NOT stored on the key.
For example, invent a new easy-to-type short #password that you type manually at the end every time you use the stored portion.
PS-2. Yubikeys were openSourced until version 4, but they are now no longer that, being proprietory since v4, as opposed to others like the #Nitrokey, which is #openSource.
As it is inconcievable with trustworthy, #verifiable #securityAudits without #openSource, many of us are now moving away from the beloved Yubikeys, or at least staying behind and only using the older versions that are actually openSourced. It is still possible to get hold of older versions.
Ref. https://www.yubico.com/2016/05/secure-hardware-vs-open-source/