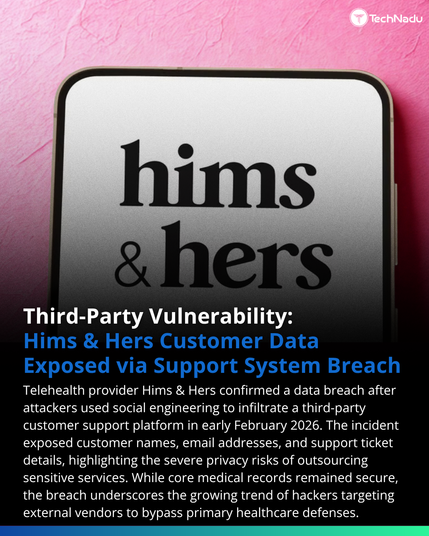
Meta paused work with a $10B AI data vendor after hackers poisoned an open-source Python library called LiteLLM and walked out with four terabytes of data. So, that's bad. And the worst part? The stolen data might include the actual training methodologies that Meta, OpenAI, Anthropic, and Google paid billions to develop. Think about what that means. You can't protect your crown jewels if they're sitting inside a vendor who's connected to your three biggest competitors, all sharing the same open-source tools, all exposed by the same 40-minute window on PyPI before anyone noticed.
🎯 The attack chain here is worth understanding: hackers compromised a security scanner called Trivy, used that access to get credentials for a LiteLLM maintainer, then published two malicious package versions that lasted less than an hour before removal. Forty minutes. That's all it took.
💼 Mercor is not some sloppy startup. It's 22-year-old founders, $500M annualized revenue, and clients at the very top of the AI industry. Sophistication doesn't protect you from a poisoned dependency you never thought to audit.
🔍 The question I'd be asking right now if I were a CISO at any of these labs isn't "were we breached." It's "how many vendors in our training pipeline are running LiteLLM, and did we even know?"
Most companies audit their own software. Almost nobody audits the software their vendors use to build the data they're buying.
https://thenextweb.com/news/meta-mercor-breach-ai-training-secrets-risk
#Cybersecurity #AIRisk #SupplyChainSecurity spc #security #privacy #cloud #infosec #ThirdPartyRisk