#Perl doyen Randall Schwartz published 6/3/26 "The Day I Decided Never to Learn Python"
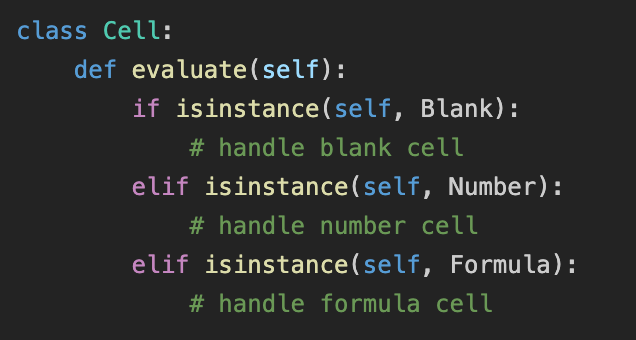
"...the fundamental mismatch in our engineering philosophies became clear.
I realized that Python's architectural foundation did not prioritize robust software contracts, explicit interfaces, or standard object-oriented design patterns. Instead, it relied heavily on dynamic dictionary workarounds, procedural dispatch, and runtime inspections."
https://medium.com/@realmerlyn/the-day-i-decided-never-to-learn-python-2c59d1a1edc5 resonates
with me.