🚀 OhMyPCAP 4.0.0 is HERE!
The ultimate FOSS PCAP analyzer just got a massive upgrade for deeper file intelligence.
New in v4.0:
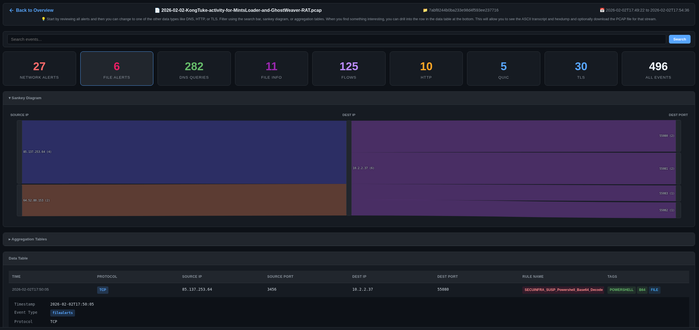
• Upgraded to YARA Forge Full ruleset — more comprehensive malware & threat detection
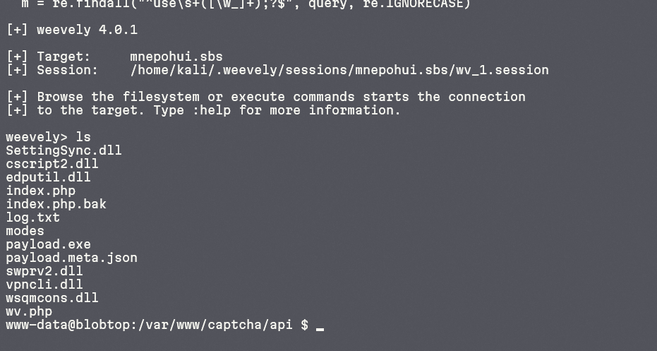
• Exiftool + rich file metadata analysis — get more file information even if there are no YARA matches
All the power you love is still here:
Suricata alerts, file alerts, Sankey diagrams, full-text search, ASCII transcripts, hexdumps, stream carving + single Docker/Podman container (perfect for air-gapped or quick spins).
Ideal for malware analysis, incident response, threat hunting, forensics & teaching.
Who’s pulling this version right now? Drop a ❤️+ reply with your main use case (malware samples? CTFs? real-world incidents? teaching?)
#PCAP #DFIR #Cybersecurity #Infosec #BlueTeam #ThreatHunting #Suricata #YARA #MalwareAnalysis
@chrissanders88 @lennyzeltser