New write-up: Weak SecOps exposed a ClickFix admin dashboard.
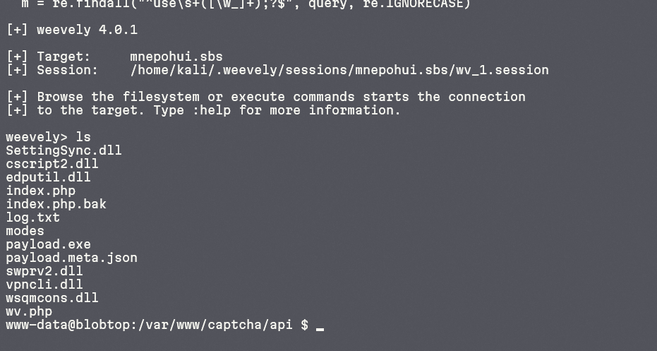
This investigation highlights exposed backups, hardcoded API keys, weak upload validation, and how stolen WordPress credentials were used to spread malware in a worm-like ClickFix campaign that is still active.
Read here:
https://potato.id/en/posts/weak-secops-exposed-clickfix-dashboard/
#CyberSecurity #Infosec #DFIR #ThreatIntelligence #ThreatHunting #IncidentResponse #MalwareAnalysis #WebSecurity #WordPressSecurity #OSINT #C2 #MalwareCampaign #SecOps #tech