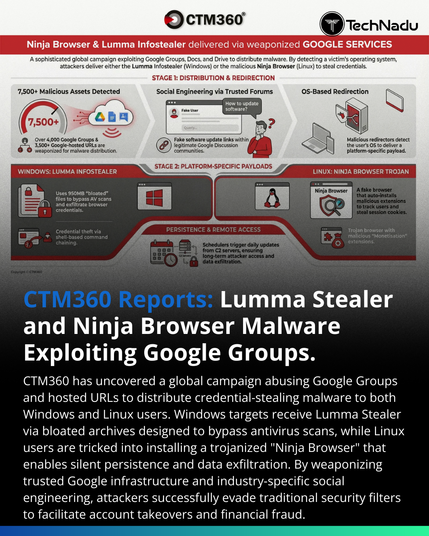
CTM360 identifies an active campaign leveraging Google Groups and Google-hosted redirect chains to deliver Lumma Stealer (Windows) and a trojanized Chromium fork branded “Ninja Browser” (Linux).
Technical highlights:
• 950MB padded executable (null-byte inflation)
• AutoIt loader reconstruction
• Memory-resident payload execution
• Multipart/form-data POST exfiltration
• Malicious extension “NinjaBrowserMonetisation”
• XOR + Base56-like JS obfuscation
• Scheduled task persistence
• Russian search engine default modification
This campaign reinforces a critical shift: SaaS platforms are now delivery infrastructure.
Defensive priorities:
– IoC blocking at firewall + EDR
– Redirect chain inspection
– Extension audit controls
– Endpoint scheduled task monitoring
How are you adjusting detection engineering for SaaS-based malware distribution?
Engage below.
Source: https://www.ctm360.com/reports/ninja-browser-lumma-infostealer
Follow @technadu for ongoing threat intelligence coverage.
#ThreatIntel #MalwareResearch #DetectionEngineering #SOCOperations #EDR #CloudSecurity #SaaSAbuse #LummaStealer #LinuxThreats #CTM360 #IncidentResponse