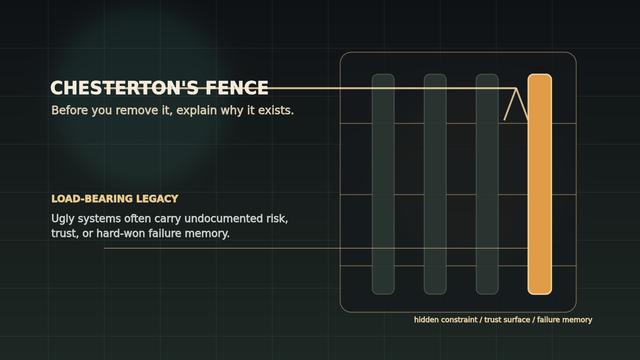
Chesterton's Fence: The Product Leader's Test for Load-Bearing Legacy
Chesterton's Fence is a product leader's test for legacy systems: before you remove the ugly process, code path, or ritual, understand the failure it was built to stop.
https://ryanw.eu/field-notes/chestertons-fence-load-bearing-legacy/