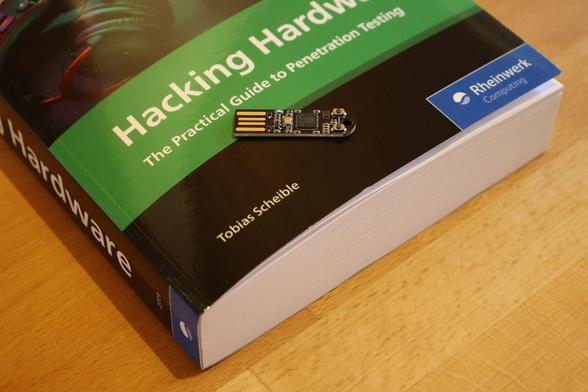
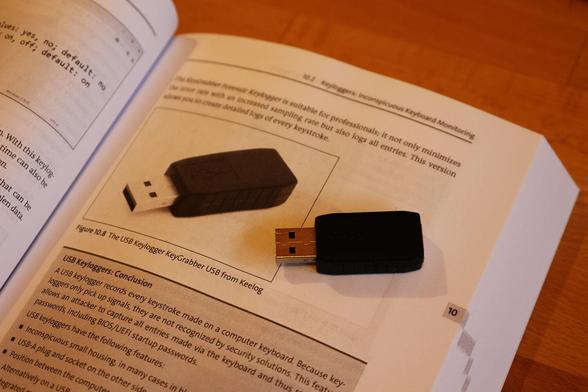
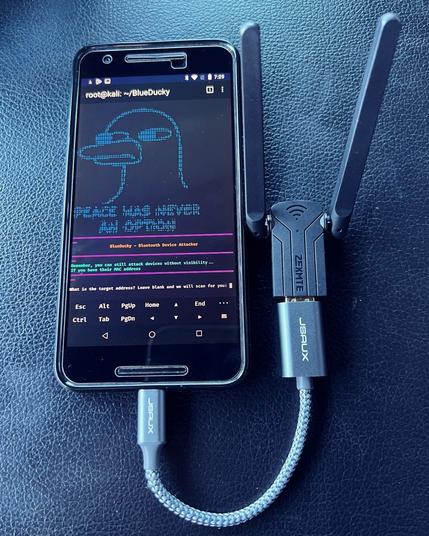
Selbst die beste IT-Sicherheitsarchitektur nützt wenig, wenn jemand einfach ein manipuliertes Ladekabel einsteckt. Genau dieses Problem war mein Antrieb für „𝗛𝗮𝗰𝗸𝗶𝗻𝗴 𝗛𝗮𝗿𝗱𝘄𝗮𝗿𝗲”, eine Übersetzung meines deutschsprachigen Buches „𝗛𝗮𝗿𝗱𝘄𝗮𝗿𝗲 & 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆”. In der Cybersicherheit konzentrieren wir uns stark auf Netzwerke und Software, aber der physische Angriffsvektor wird oft fatal unterschätzt.
In meinem neuen englischsprachigen 𝗕𝘂𝗰𝗵 zeige ich euch praktisch und detailliert, wie diese Angriffe funktionieren und wie man sich davor schützt. 🧰
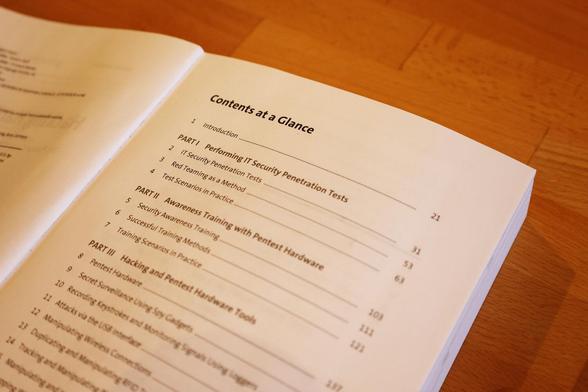
Egal, ob ihr im Red Team seid und euer Arsenal erweitern wollt oder im Blue Team arbeitet und diese Vektoren verstehen müsst – dieses englischsprachige Buch liefert euch die Praxis. 🛠️
#RedTeam #BlueTeam #KeystrokeInjection #SDR #InfoSec #CyberSecurity #Hard