𝗘𝘃𝗶𝗹𝗖𝗿𝗼𝘄 𝗞𝗲𝘆𝗹𝗼𝗴𝗴𝗲𝗿 - 𝗗𝗲𝗿 𝗞𝗲𝘆𝗹𝗼𝗴𝗴𝗲𝗿 𝗳𝘂̈𝗿 𝗡𝗲𝗿𝗱𝘀 ⌨️
Der typische Hardware-Keylogger ist darauf ausgelegt, möglichst einfach zu funktionieren. Meist genügt es, ihn einzustecken und loszulegen. Zum Auslesen der Daten muss lediglich eine bestimmte Tastenkombination betätigt werden, um sie in einer TXT-Datei zu speichern.
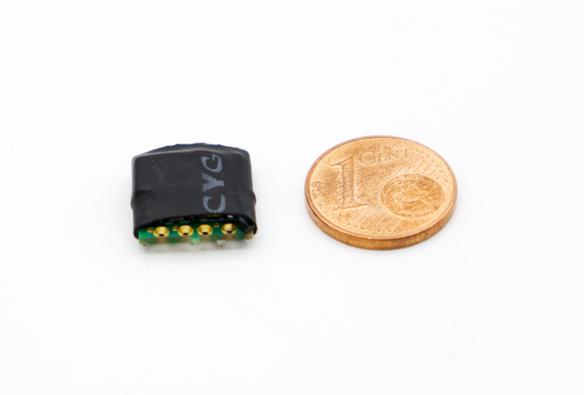
Der EvilCrow Keylogger ist anders. Er basiert auf einem Atmega32U4 mit Arduino-Lilypad-USB-Bootloader, einem ESP32-PICO für die WLAN-Kommunikation und einem MicroSD-Kartenleser. Die Software dazu ist auf GitHub zu finden.
Eigenen Projekten steht nichts im Wege 😉