The data that I didn’t know I didn’t have to back up to Microsoft’s cloud
I spent more time than I’d planned Friday afternoon poking around the security settings of my Windows laptop, then undoing one setting that I am somewhat embarrassed to admit I had scarcely thought about over the previous two and a half years of using this HP.
The FBI gets some credit for that for making me rethink my own device security after some of its agents raided Washington Post reporter Hannah Natanson’s home two weeks ago and seized several of her devices–an obvious move to intimidate journalists– leaving the storage encryption on that hardware as the last line of defense for her data.
Forbes security writer Thomas Brewster gets the rest of the credit for a strong post Friday morning unpacking how Microsoft’s approach to device encryption via its BitLocker software can leave Windows computers open to law enforcement investigators who bring a valid legal order to the company requesting a particular user’s encryption recovery key.
“It’s possible for users to store those keys on a device they own, but Microsoft also recommends BitLocker users store their keys on its servers for convenience,” Brewster wrote. “While that means someone can access their data if they forget their password, or if repeated failed attempts to login lock the device, it also makes them vulnerable to law enforcement subpoenas and warrants.”
He reported that Microsoft gets about 20 requests a year for BitLocker keys but cannot respond to many of them because the customers involved didn’t back up those keys to its cloud.
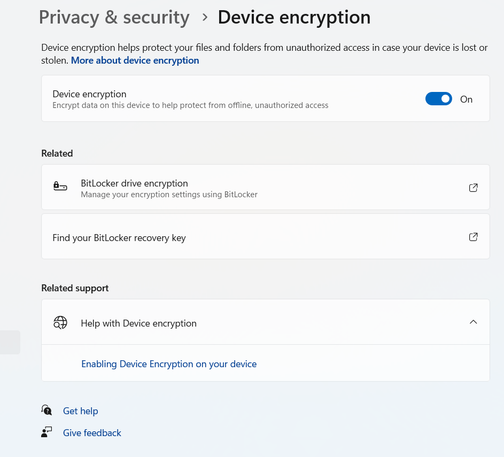
Windows 11 Home’s Device Encryption isn’t branded as BitLocker in the Settings app, but it runs on the same framework. And as in the Pro, Enterprise and Education editions of Windows 11, it allows a choice of key-backup locations–which I did not realize until eyeballing Microsoft’s documentation after I’d read Brewster’s post.
I had gone unthinkingly with the default of having the recovery key backed up to my Microsoft 365 cloud storage; I don’t remember even being presented with a choice when I set up the computer in August of 2023. But since the key is only a string of 48 numbers periodically separated by dashes, there was no point in keeping it there.
Instead, I saved it in my end-to-end-encrypted password manager 1Password, where the security design does not expose backdoors that can be opened with a court order. Then I deleted the backed-up recovery key from my M365 storage after clicking a checkbox to confirm that I’d saved the key elsewhere–along with seven older ones I found saved there, going back to a Surface laptop I reviewed a decade or so ago.
(I don’t know how long it will take for this data to be gone from my online storage, although there is the option of decrypting and re-encrypting the laptop to ensure the old key is useless.)
I never should have taken Microsoft up on this offer. But Microsoft should not be leaving users in this position–as Johns Hopkins University cryptography professor Matthew Green told Brewster in that article. Apple’s FileVault device encryption now automatically encrypts recovery keys backed up to the company’s iCloud service (see this explainer from my friend Glenn Fleishman at Six Colors), leaving nothing for a third party to inspect with a warrant.
There are many areas where Microsoft can’t readily catch up with Apple, starting with having a mobile platform to complement its desktop operating system. But this should not be one of them.
#BitLocker #diskEncryption #encryption #FBI #HannahNatanson #keyEscrow #M365 #Microsoft365 #MicrosoftBackup #Windows11Home #WindowsDeviceEncryption