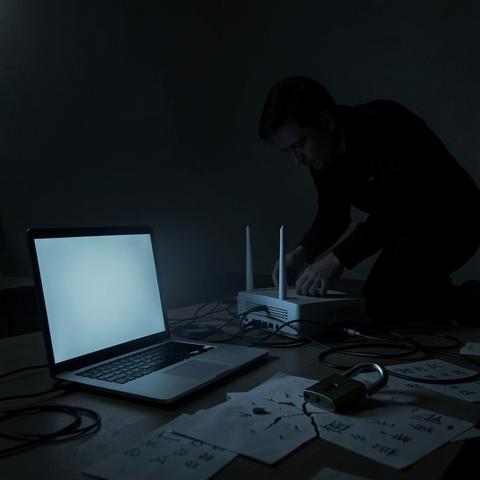
Operation Masquerade проводилась в березні 2026 року і полягала у відновленні роутерів, хакнутих російськими хакерами з групи #APT28. Ця група, відома також під назвою #FancyBear, працює на російське #ГРУ, протягом 2025 року взяла під контроль тисячі роутерів #TPLink, які містили незалатані діри, і використовувала їх для перехоплення трафіку користувачів.
#hackers #cybersecurity