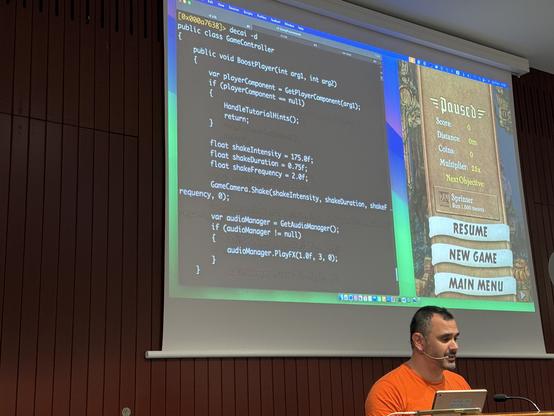
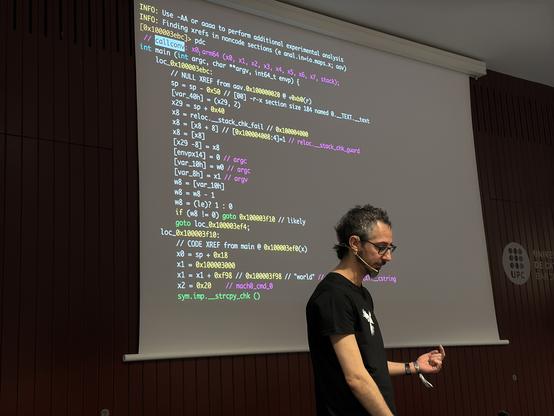
Decai decompiling a malicious shellcode.
The instructions are not so readable, if you're not used to syscalls int 0x80. AI does it for you.
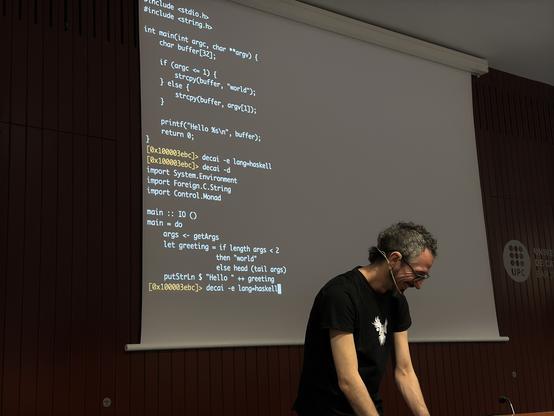
A blog post on r2ai / decai by @pancake which shows decompiling to Swift :
https://www.nowsecure.com/blog/2025/01/29/decompiling-apps-with-ai-language-models/
r2ai solves my CrackMe in a few seconds. It's both elegant and educational.
Read this: https://cryptax.medium.com/cracking-my-own-crackme-with-r2ai-5629bcc7d5fe
And view @dnakov video at r2con: https://www.youtube.com/watch?v=UxE5GNUBCXo
cc: @radareorg
I've been running decai with Claude AI on a malware named Goldoon.
Ghidra is usually quite good to decompile, but just compare the decompiled output with r2 (@radareorg) decai/Claude and ghidra!
This is marvelous. So much clear and concise + Claude immediately thought this was malicious (I didn't hint anything).
NB. I will talk about this at @1ns0mn1h4ck
@radareorg the program was implemented using Swift, which does not disassemble very nicely. So, I tried decai. Output in C wasn't nice, but output in Java is quite usable. At least, the password is very visible.
(But don’t use it for cheating, you know 😜)
#r2con2024
They were really helpful in @as0ler’s, combining them in the process.
#r2con2024
#r2con2024
And with -Q command you can also ask if the code is vulnerable and where, and it will answer that! Isn’t it awesome?
#r2con2024





 radare
radare