This account does not represent my employer.
@cryptax
- 878 Followers
- 361 Following
- 2K Posts
This account does not represent my employer.
A talk is short (especially that we had to merge in our ideas, with @virtualabs !) and there are a couple of thoughts and feedback form results of @ph0wn that I never got the chance to present. So, I made a blog post about it, it's interesting to you if "CTF and AI" is a problem to you and you want to think about it.
https://cryptax.github.io/posts/ctf-ai/
cc: @cpu
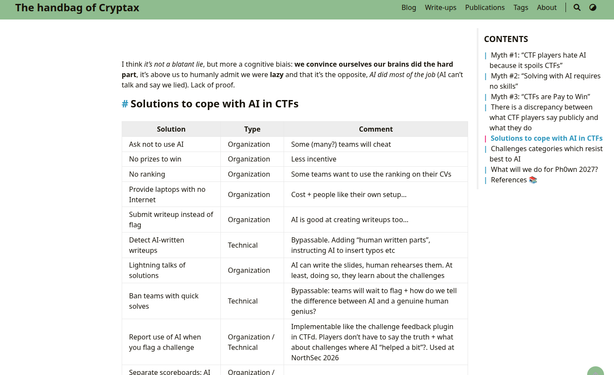
CTFs and AI
CTFs and Artificial Intelligence. Post Ph0wn 2026 Thoughts. Myth #1: “CTF players hate AI because it spoils CTFs” Reality: this is not the opinion of the majority of CTF players “AI has destroyed CTFs” - this kind of message is frequent on the net. However, in a feedback form of Ph0wn CTF 2026, 80% hold no grudge against AI and are either happy with it, or just want to adapt:
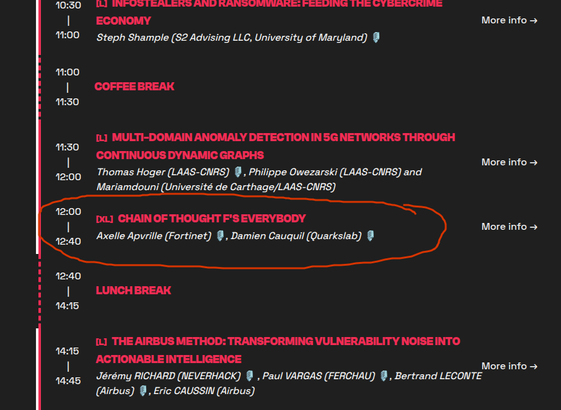
Today, @virtualabs and I presented at THCon about the vast problem of AI and CTFs. It led to interesting discussions, and we were very happy with everybody's concern and enthusiasm.
https://thcon.party/events/#chain-of-thought
https://tagazok.virtualabs.fr/thcon/
Our session has been live streamed, our slides have been uploaded if you want them + we've been interviewed by a local radio, @cpu
"A University in the US was hit 3 times by ransomware" (approximative quote) because they pay, get their data back, recover... But forget to patch, so they are hit by another instance.
Love this talk at THCon by Steph Shample.
#ransomware #infostealers #2026 #thcon
Slides > silence.
Community > silos.
10 > 9.
Got research, real-world insights, or a hands-on workshop? Bring it to the stage for the 10th edition of BSides Munich.
Submissions for #BSidesMunich2026 are now open.
Submit your idea and dig into the details:
https://2026.bsidesmunich.org/cfp
#BSidesMunich2026 #CFP #BSidesMunich
https://social.bsidesmunich.org/submissions-for-bsidesmunich2026-are-now-open/
We're speaking at THCon, with @virtualabs on Wednesday this week.
AI has really changed CTFs. Can we do something about it? Yes. We'll present a couple of ideas we experimented with - and hope it gives you tons of other ideas.
If you can't make it to Toulouse this wednesday, the conference is streamed if I'm correct.
BTW, don't run the exploit without understanding, in particular, you should **backup** your su. Something with cp -a su su.orig.
You'll see the exploit is devastating, because it gets rid of the password protection, but you don't see anything on the disk : the binary looks the same, original size, original date.
Devastating privilege escalation on Linux: https://copy.fail/
Explanation: https://xint.io/blog/copy-fail-linux-distributions
Implementation in Go: https://github.com/badsectorlabs/copyfail-go
... and I learned today that there are AF_ALG socket types, to access cryptographic functions of the kernel.
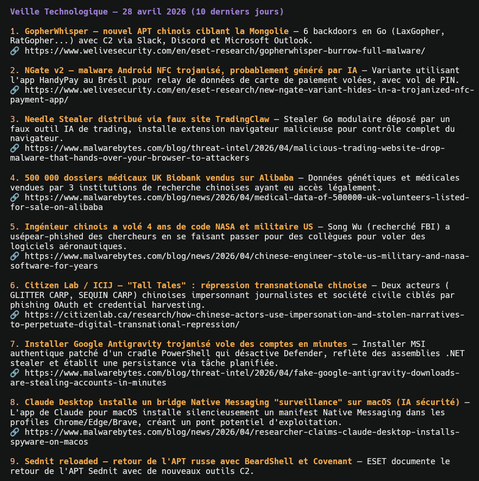
Just created a techno watch skill that I use with OpenCode + our in-house LLM.
I told the skill what it should look for, my preferred list of websites (but not limited to that) and I got very very decent output with plenty of links I want to look into.
It's in French, sorry.
NGate v2: Android malware with "parts probably generated by AI" (well, hell, yes, like most apps now...)
Actually, the code snippet marked as AI isn't with certain attribution to AI. But possible.