J'ai publié la note « Setup Fedora CoreOS avec LUKS et Tang »
Had one of those days of problem chains today. I've rebuilt #homelab internal CA over the past two weeks, and today I wanted to do the simple task of making my #truenas scale server get it's web certificate from it over acme.
Well problem one, truenas doesn't do acme via anything other than dns challenges, which I haven't setup internal dns for yet. So (given my Truenas was still running 24.04) I decided to upgrade it to 24.10 to see if that added any functionality. The upgrade was smooth, but it once again broke my #clevis automatic unlock of my storage pool.
So then I decided to fix my unlock script to cleanly handle updates (and fixed it so that pool passwords could contain " while I was at it, because why not)
Then having fixed that, I decided I should update my blog post (https://i.am.eddmil.es/posts/clevis-tang-truenas-scale/) about it from last year with the new more robust script.
I then realised when I'd updated all my firewall rules last month, I'd broken ssh access from my #forgejo runner to my webserver used for auto deploy website updates, so I had to fix the #puppet that controls the firewall rules.
Finally that was all working, so I updated my truenas to 25.04, in the vain hope that would have better acme support (it doesn't, but at least it validated my clevis script updates, and was the only thing today that just worked as intended)!
Finally I hacked something hideous together using https://github.com/danb35/deploy-freenas/ and acme.sh to get a certificate from my acme server and deploy it (which I could have done at the start and skipped the whole day fixing other problems)
Taking 6 hours to deploy an SSL cert wasn't quite what I had planned for my Easter Sunday, but at least I achieved it in the end. Onwards to see what chaos I can cause tomorrow...
Clevis and Tang with Truenas Scale
Introduction This post has been updated since launch, with modified instructions for Truenas Scale versions >=24.04, and again with an improved unlock script This is a quick-and-dirty follow up to my Clevis and Tang mostly for my own reference later, but I thought I’d add it here in case it can be of use for anyone else. As part of my ongoing migration-off-closed-systems, I want to remove my QNAP Nas and move to something self-built on Truenas Scale. However I ideally want the same Data-At-Rest encryption with automatic network-based unlock that my servers have. This is my quick hack to make this work, that I should revisit later and make more robust.
Could it be that #clevis has a bug that the following ends up failing unless the passphrase is non-empty?
sudo clevis luks bind -d /dev/nvme... tpm2 '{"pcr_ids":"1,4,5,7,9"}'
An empty passphrase can be created by the means of:
sudo cryptsetup luksChangeKey --force-password /dev/sda3
It is a totally legit configuration for NUC7CJYH, which I use for kernel testing.
@Gentoo_eV Given that I get a KVM console in time, I will demonstrate my installation guide (https://gentoo.duxsco.de/) in English using a #Hetzner dedicated server.
- What? Beyond Secure Boot – Measured Boot on Gentoo Linux?
- When? Saturday, 2024-10-19 at 18:00 UTC (20:00 CEST)
- Where? Video call via BigBlueButton: https://bbb.gentoo-ev.org/
The final setup will feature:
- #SecureBoot: All EFI binaries and unified kernel images are signed.
- #MeasuredBoot: #clevis and #tang will be used to check the system for manipulations via #TPM 2.0 PCRs and for remote LUKS unlock (you don't need tty).
- Fully encrypted: Except for ESPs, all partitions are #LUKS encrypted.
- #RAID: Except for ESPs, #btrfs and #mdadm based #RAID are used for all partitions.
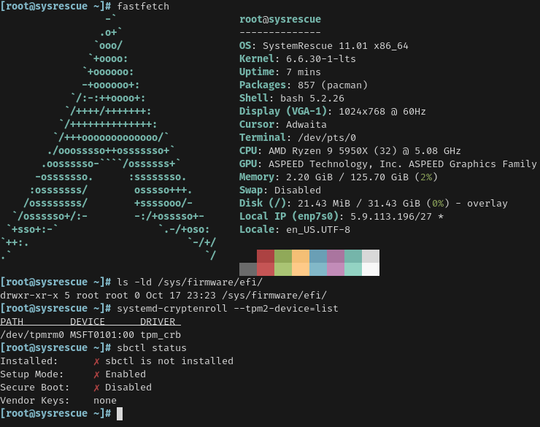
- Rescue System: A customised #SystemRescue (https://www.system-rescue.org/) supports SSH logins and provides a convenient chroot.sh script.
- Hardened #Gentoo #Linux for a highly secure, high stability production environment.
- If enough time is left at the end, #SELinux which provides Mandatory Access Control using type enforcement and role-based access control
Just setup Clevis to automatically decrypt LUKS volumes using TPM2. This is the script I used to set it up on an Ubuntu VM in Proxmox:
https://gist.github.com/heywoodlh/b55eb33e248db2b8a7625c1fddc6b8d3
@mirabilos: Whoa, that phrasing is dangerous. Without the word "just" it would have meant the opposite.
Already any experience regarding the usage of #clevis (and #tang) for unlocking full disc encryption over #IPv6?
After a request on the #selfhosted community on Lemmy, I wrote up how I use LUKS, Clevis, and Tang to give me network-bound encryption. This means that I can restart my servers as long as they're on my home network without worrying about having to log in to decrypt the drive, but if someone breaks in and steals my servers and turns them on anywhere else, the data on them is safe. https://i.am.eddmil.es/clevistang/
 gihyo.jp
gihyo.jp