#InfoSec #CyberSecurity #Pentesting #BugBounty #OffSec #SupplyChain
#InfoSec #CyberSecurity #Pentesting #BugBounty #OffSec #SupplyChain
https://www.techradar.com/pro/security/they-mopped-the-floor-with-me-and-pulled-every-childish-game-they-could-disgruntled-researcher-releases-second-major-windows-zero-day-claims-microsoft-would-ruin-my-life-and-they-did #cybersecurity #Microsoft #BugBounty #vulnerability #disclosure
How I Turned an AI Search Endpoint into an Internal Org Intel Leak
This vulnerability was an authentication bypass and data leak involving an AI search endpoint acting as an oracle. The application failed to implement rate limiting, exposing presigned AWS S3 URLs without authentication to clients. Bypassed rate limits and enumerated valid prefixes, the researcher discovered a blueprint containing internal organization IDs, program eligibility logic, operational flags, system behavior hints—essentially a comprehensive system map. The researcher proposed adding strict rate limiting, revoking all existing presigned URLs, proxying requests through the backend, returning only necessary fields, sanitizing S3 payloads, removing internal metadata fields, adding logging and anomaly detection for enumeration patterns as mitigation measures. Key lesson: Combinations of seemingly minor flaws can lead to scalable vulnerabilities that provide a detailed system map #BugBounty #WebSecurity #DataLeak #APISecurity #RateLimiting
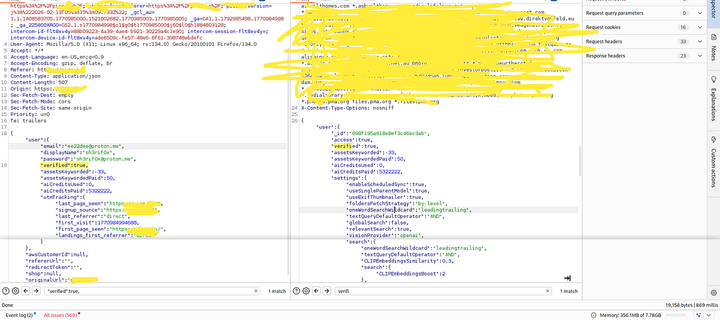
Email Verification Bypass & AI Credits Manipulation via simple Mass Assignment
This vulnerability was an Authentication Bypass through a Mass Assignment flaw in the application's registration functionality. The server returned sensitive fields in response to a normal registration request, including verified, aiCreditsPaid, aiCreditsUsed, assetsKeyworded, and settings. By reusing the initial response and modifying sensitive values directly within the request, the researcher bypassed email verification (verified: false ➡️ verified: true), manipulated AI credits (aiCreditsPaid: 50 ➡️ aiCreditsPaid: 5322222, aiCreditsUsed: 0), and controlled multiple internal user attributes. This vulnerability had critical impacts such as bypassing email verification, unlimited AI credits, full control over user internal attributes, and abuse of platform features at scale. The root cause was trusting client-side input, no validation on sensitive fields, and direct binding of request to the user object (Mass Assignment). Proper remediation includes validating sensitive fields, sanitizing user input, and separating bound objects in the application logic. Key lesson: Analyze server responses carefully as they can reveal everything you need to exploit Mass Assignment bugs. #BugBounty #Cybersecurity #WebSecurity #AuthenticationBypass #MassAssignment
Complete Guide to JWT Vulnerabilities: Detection, Exploitation, and WAF Bypass
This article outlines the fundamentals of JSON Web Tokens (JWTs) and common attack methods like key confusion. The researcher explains how to identify weaknesses in validators by examining their response to noisy payloads (Signature Resilience), exploiting poorly implemented libraries that crash instead of returning a 401 error for invalid tokens. JWT structure consists of three parts: Header, Payload, and Signature. Key takeaway: Validate JWTs carefully to avoid security vulnerabilities. #BugBounty #WebSecurity #JSONWebTokens
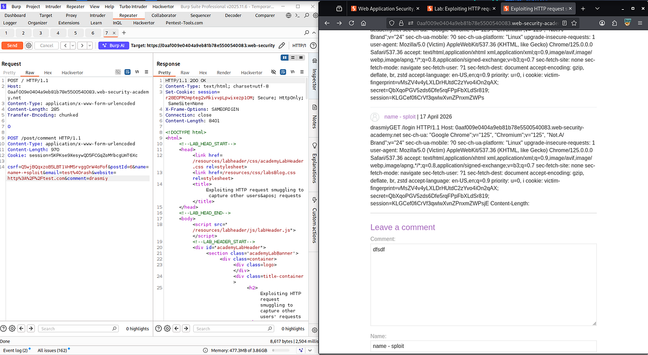
Exploiting HTTP Request Smuggling to Capture Other Users’ Requests | khan sploit | Mo Rashid
This vulnerability is an Information Disclosure through HTTP request smuggling. The application server failed to handle multiple requests concurrently, leading to the intermingling of user requests. By sending two malicious requests simultaneously—a comment post and a cookie-grabbing request—the attacker exploited this flawed handling logic, causing the server to send the response for both requests in a single response. The researcher was then able to capture the victims' cookies by observing the responses for the cookie-grabbing request. This information disclosure allowed unauthorized access to other users’ sessions. The researcher did not disclose a payout amount, but the article mentions that they reported the vulnerability to HackerOne and received recognition from Khan Academy. To remediate, implement request parsing logic that correctly handles multiple concurrent requests and separates them before processing—never trust user-controlled headers for security decisions. Key lesson: Validate and separate concurrent requests to prevent HTTP request smuggling. #BugBounty #WebSecurity #InformationDisclosure
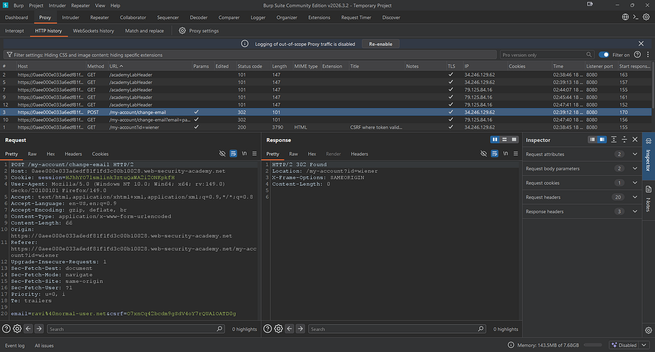
Day 5 — CSRF Token Bypass using GET Request
This article discusses a Cross-Site Request Forgery (CSRF) vulnerability where an attacker can bypass CSRF tokens by manipulating GET requests. The root cause is inconsistent validation of CSRF tokens across HTTP methods, particularly on GET requests. In this case, the application incorrectly validated CSRF tokens for GET requests but did so correctly for POST requests. By modifying a legitimate request to use the GET method and moving parameters into the URL, the researcher discovered that the server did not validate the CSRF token. The attack involves creating an HTML PoC (proof-of-concept) with JavaScript to automatically submit the modified request, exploiting the victim without their interaction. This vulnerability emphasizes the importance of consistent validation for CSRF tokens across all HTTP methods. Key lesson: Validate CSRF tokens consistently regardless of HTTP method to maintain security. #BugBounty #WebSecurity #CSRF #VulnerabilityResearch
https://smartpicks4u.medium.com/day-5-csrf-token-bypass-using-get-request-791cba29812d?source=rss
HyveGuardrd public security challenge
Built a consensus-gated server defence with AI. FROST threshold crypto, Merkle verification, MPC rotation, post-quantum hybrid, honey tripwires, DAG audit.
Four servers, four jurisdictions. Eight mechanisms. One key that exists nowhere.
hyveguard.com
#infosec #ctf #security #cryptography #pentesting #hacking #bugbounty #redteam #netsec #thresholdcrypto #postquantum #ed25519 #zerotrust #threatresearch
Before the #vulnpocalypse, there will be the #vulnslopalypse.
As someone who has dealt with vulnerability reports in all shapes, forms and levels of veracity for at least a decade, I posit that's where we will hurt the most, for the longest time, and without reaching symmetry.
For the old farts: remember the burpsuite #bugbounty submissions? That, but at unprecedented scale, and these you can't easily filter out.
#vulnpocalypse #Mythos #infosec #vulnerability #vulnslopocalypse
Disclosure: This was Rippling (rippling.com)
Essentially, the flaw I discovered was that if you use their platform to send someone a job offer via email, shortly after sending said offer (no interaction required on the part of the recipient, such as, say, actually looking at or accepting the offer), if that person already had a Rippling account, such as from a prior employer, a Rippling process would run that would populate their information from what was already in the Rippling backend from another tenant.
This info includes all the PII, including SSN, banking, address etc.
That info would automatically become visible to the Rippling user who had sent the job offer email.
So, all you needed was a rippling tenant, and if your target had previously used Rippling ever - you could exchange their email address for all the info.
Timeline: reported in July 2025 to the Rippling Bugcrowd bug bounty program, accepted as a critical issue within 48 hours, only fixed last week (9 months).
No bounty was offered.
Just a data point for anyone else who considers submitting to this program. Probably the least impressive bug bounty experience I’ve had in the last 15+ years.