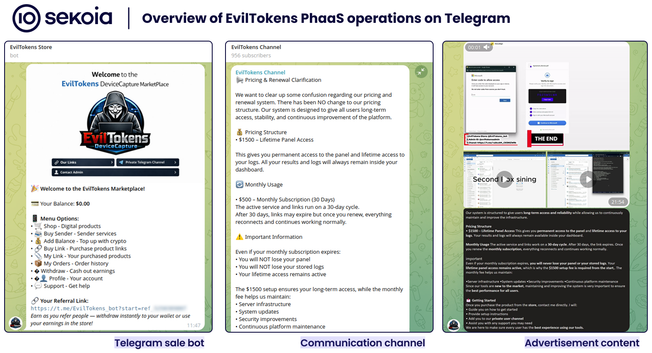
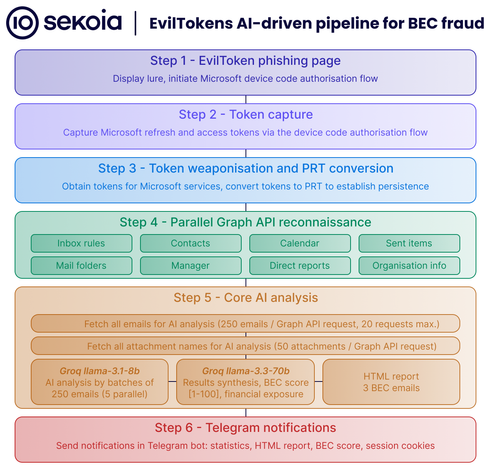
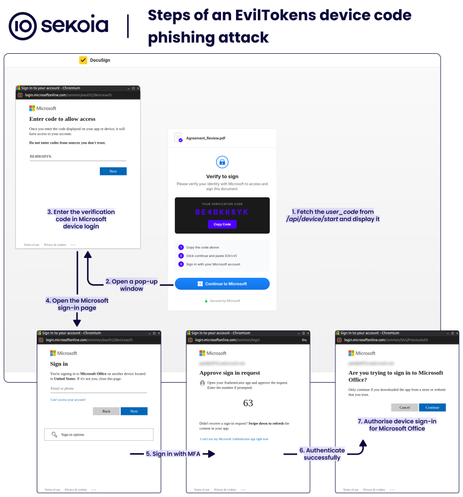
Part 2 of our #EvilTokens analysis is live. TDR analysts uncovered the AI-augmented features that automate and scale #BEC workflows, marking a breakthrough in the #PhaaS ecosystem.
| Website | https://sekoia.io |
| Blog | https://blog.sekoia.io |
| GitHub | https://github.com/SEKOIA-IO |