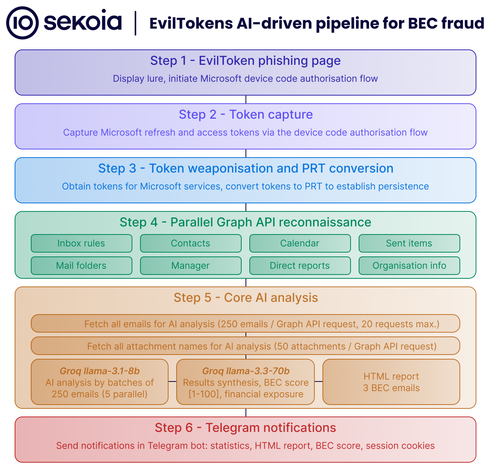
📢⚠️🪝Watch out, hackers are using #CalPhishing (Calendar Phishing) with the EvilTokens phishing kit to exploit #Outlook calendar invites and device code phishing to steal #M365 session tokens and breach enterprise accounts.
Read: https://hackread.com/calphishing-eviltokens-kit-outlook-invites-m365/