Es mas rapido, chiquito (no dependencias) y directo que la famosa SDL, pero al precio de escribir mas, es mas complejo por que expone el subsistema X sin pudor! , y lo peor , muy poca documentacion ! Y ni la IA te salva ! Cual es mi meta (ya perdida) ? escribir el backend de la libreria Nuklear solo en xcb, luego usar la como interfaz para otro proyecto mas loco tipo juego Cataclysm DDA o Space Station 13 (MMORPG)... Pero casi seguro va derecho al cementerio. Pero es la diversion (o locura?) de hacer que aparezca algo en pantalla y se mueva... terrible.... #xcb #graphics #x11 #xlib #linux #gui
Es mas rapido, chiquito (no dependencias) y directo que la famosa SDL, pero al precio de escribir mas, es mas complejo por que expone el subsistema X sin pudor! , y lo peor , muy poca documentacion ! Y ni la IA te salva ! Cual es mi meta (ya perdida) ? escribir el backend de la libreria Nuklear solo en xcb, luego usar la como interfaz para otro proyecto mas loco tipo juego Cataclysm DDA o Space Station 13 (MMORPG)... Pero casi seguro va derecho al cementerio. Pero es la diversion (o locura?) de hacer que aparezca algo en pantalla y se mueva... terrible.... #xcb #graphics #x11 #xlib #linux #gui
👉 https://ia.cr/2024/1554
#IEEE #Standardization #XCB #XCB_AES #cosic #kuleuven
Breaking the IEEE Encryption Standard – XCB-AES in Two Queries
Tweakable enciphering modes (TEMs) provide security in various storage and space-critical applications, including disk and file-based encryption and packet-based communication protocols. XCB-AES (originally introduced as XCBv2) is specified in the IEEE 1619.2 standard for encryption of sector-oriented storage media and comes with a formal security proof for block-aligned messages. In this work, we present the first plaintext recovery attack on XCB-AES $-$ the shared difference attack, demonstrating that the security of XCB-AES is fundamentally flawed. Our plaintext recovery attack is highly efficient and requires only two queries (one enciphering and one deciphering), breaking the claimed $\mathsf{vil\text{-}stprp}$, $\mathsf{stprp}$ as well as the basic $\mathsf{sprp}$ security. Our shared difference attack exploits an inherent property of polynomial hash functions called separability. We pinpoint the exact flaw in the security proof of XCB-AES, which arises from the separability of polynomial hash functions. We show that this vulnerability in the XCB design strategy has gone unnoticed for over 20 years and has been inadvertently replicated in many XCB-style TEM designs, including the IEEE 1619.2 standard XCB-AES. We also apply the shared difference attack to other TEMs based on XCB $-$ XCBv1, HCI, and MXCB, invalidating all of their security claims, and discuss some immediate countermeasures. Our findings are the first to highlight the need to reassess the present IEEE 1619.2 standard as well as the security and potential deployments of XCB-style TEMs.
And then, of course, it's very different from #Xt. It strictly requires #XRender, using its "picture" objects as the primary drawing handle, and just offering the core X11 "drawable" on demand. It strictly requires a "true color" visual. It has NO support whatsoever for core drawing primitives and core (bitmap) fonts. It doesn't create a window for every widget but instead manages widgets fully client-side ... all these are probably not "blockers" but just how you'd design a GUI toolkit for X11 nowadays 😉
I need your help, please! 😁
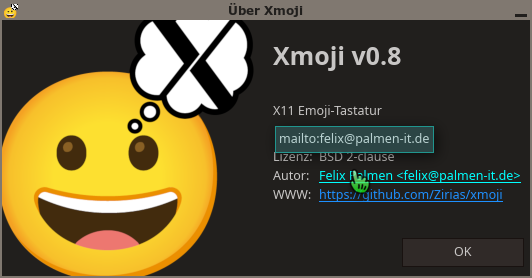
Xmoji 0.8 introduced an important part for #i18n, translations. But I'm not exactly fluent in many languages. Please, if you can, help me translate! The process is documented in https://github.com/Zirias/xmoji/blob/master/TRANSLATE.md . If there are any issues with these instructions, please let me know.
Xmoji aims to be the "best" tool to input emojis with "pure" X11:
- Written in plain #C, with minimal dependencies
- Uses #Xrender for its UI, communicates with the X server using #xcb
- Offers two methods for input: Faked keyboard events or the "primary selection"
- Has a search tab and a list of recently used emojis
- Customizable appearance using X resources
- Several options to configure key injection and the search method
Roadmap to V1.0:
- Optional single-instance mode
- Optional tray icon
#X11 #emoji #keyboard
#xcb #development thoughts:
One of the features I'd like to add to #Xmoji is a "system #tray icon". I know these aren't "en vogue" any more, but I like the concept a lot for an application you'll typically leave running and only use from time to time, which is likely a usage pattern for an "#emoji #keyboard".
So, I found a spec based on #XEMBED, X selections and client messages (therefore, pure X inter-client communication), I think I can implement that! 👍
https://specifications.freedesktop.org/systemtray-spec/0.2/
Digging deeper, I found there's a successor called #SNI and the spec above is considered "legacy" (after only 20 years, hehe) 🤨. SNI is based on #dbus. Oh damn ... it's not that I particularly hate dbus, it probably makes a lot of sense for complex desktop environments, but I really want to keep #Xmoji "plain #X11". I'll just use the old spec. At least I found #KDE seems to have a compatibility service: xembed-sni-proxy. No idea about Gnome. But then, screw it.
System Tray Protocol Specification
1 Overview # The system tray is an application running on a given X screen that can display small icons provided by running applications. Windows XP calls this feature the notification area. [1] Inspired by KDE, this specification uses the term system tray. From a UI standpoint, the system tray is n…
Finally removed the nasty "glitches" setting from #Xmoji!
After lots of (unsuccessful) research whether I can somehow check which modules(!) are loaded on the X server (to find out whether #GLAMOR is used, which I *think* causes a bug in compositing glyphs with #XRender) ... I finally remembered an old strategy which is both horribly ugly and pretty reliable: probing!
I now do a dummy glyph compositing to a single-pixel off-screen pixmap during startup and fetch the resulting pixmap from the server, so I can simply *see* whether the result is buggy. 🙈
https://github.com/Zirias/xmoji/commit/93143775e6ad9b01f7f23b2da48c5e6921669fd0
I actually wonder why I didn't have that idea much earlier. E.g. coding on the #C64, probing the hardware (e.g. to identify VIC and SID model by their behavior) is a pretty common thing to do 🥸
In case anyone is interested, this is how this exercise looks like:
The point coordinates for the consecutively rendered triangles are in the arrays "points" (the "background") and "x1points" and "x2points" (the "X") 🤪