«Storm Infostealer umgeht 2FA — Malware übernimmt Accounts ohne Passwort:
Der neue Storm Infostealer umgeht 2FA, kapert Accounts per Session-Hijacking und entschlüsselt Daten serverseitig.»
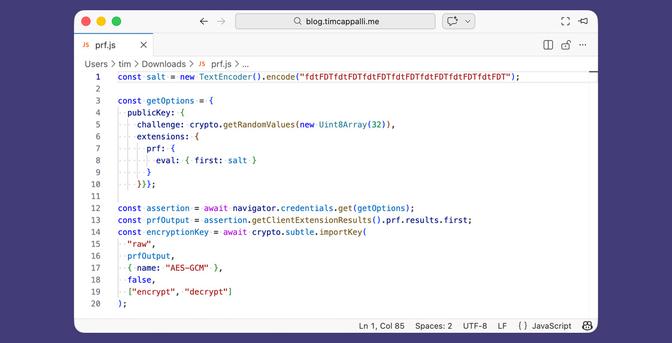
Ich gehe mal davon aus, dass die JSON Web Token (JWT) umgehen. JWT ist zwar populär aber nicht sicher. Die Zwei-Faktoren Autentifikation (2FA) ergibt am Ende auch JWT zur online Erkennung.
#2fa #jwt #login #hacking #userdata #hack #online #malware #passwort #itsec #web #internet