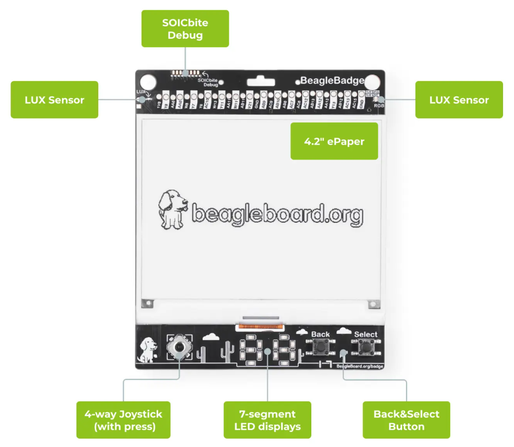
BeagleBadge wearable platform boasts TI AM62L SoC, ePaper display, and Linux support
Working With STM32 Arm TrustZone-Based Projects in CLion
#Clang #CLion #Tipstricks #Arm #Stm32 #Stm32cubemx #Trustzone
https://blog.jetbrains.com/clion/2026/03/working-with-stm32-arm-trustzone-in-clion/
➤ 透過堆疊指標數值比對,快速掌握 TrustZone 運行切換
✤ https://danielmangum.com/posts/arm-cortex-m-security-state-gdb/
在嵌入式系統開發中,調試具備 TrustZone(Armv8-M 安全擴充功能)的處理器(如 Arm Cortex-M33)常面臨一項挑戰:如何快速判斷處理器目前正處於「安全(Secure)」還是「非安全(Non-Secure)」狀態。開發者 Daniel Mangum 提供了一個簡潔高效的方案。由於處理器在不同安全狀態下會使用各自獨立的堆疊指標(Stack Pointer, SP),我們只需透過 GDB 同時讀取當前的 SP 以及各個堆疊指標變體(MSP_S, MSP_NS 等),並進行數值比對,就能即時揭示處理器的運行環境。這種方法在處理如 Zephyr RTOS 等複雜的多執行緒系統時,能顯著提升排錯效率。
+ 「這是在處理
#嵌入式系統 #Arm Cortex-M #GDB 調試 #TrustZone #韌體開發

Determining Current Arm Cortex-M Security State with GDB
In my day job and free time I frequently find myself debugging Arm Cortex-M microcontrollers (MCUs). In recent years, it has become more and more common for the cores in these MCUs to implement Armv8-M, with the Arm Cortex-M33 being a very popular variant. Armv8-M includes an optional security extension (Cortex-M Security Extension or “CMSE”), which is more commonly known by its marketing name, TrustZone. The security extension allows for a core, or a Processing Element (PE) if using the official terminology in Arm reference manuals, to divide memory into Secure and Non-Secure regions.
https://reverser.dev/linux-kernel-explorer
#ycombinator #Android_security #penetration_testing #reverse_engineering #mobile_security #TrustZone #Play_Integrity #security_audit #device_farm_testing #bootloader_security #hardware_security #Android_pentesting #firmware_analysis #TEE_security #kernel_security #Android_hardening
At BlackAlps, Marcel Busch and Philip Mao show how forgetting to check input types in the trusted apps of TrustZone leads to memory read/write.
Exploiting Android Linux kernel from Qualcomm Trustzone (QSEE) (CVE-2021-1961)
https://tamirzb.com/attacking-android-kernel-using-qualcomm-trustzone
Credits Tamir Zahavi-Brunner
A few years old but still an interesting blog post showing how to attack Mobile Trusted Execution Environments (ARM TrustZone) to extract biometric data
https://www.synopsys.com/blogs/software-security/cve-2020-7958-trustlet-tee-attack.html
Anyone here who has experience with bare-metal programming TrustZone-M applications for Nordic platforms? I have problems configuring my NSC region and I can't figure out what's wrong 😫
(please boost, I need this)
Update: Found the problem, it works now!
A few years old but still an interesting blog post showing how to attack Mobile Trusted Execution Environments (ARM TrustZone) to extract biometric data
https://www.synopsys.com/blogs/software-security/cve-2020-7958-trustlet-tee-attack.html

 Hacker News
Hacker News



