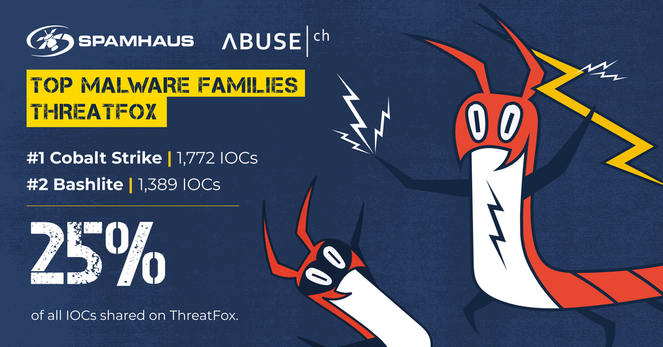
Over the past 30 days, our community shared 27,165 new #IOCs on ThreatFox 🦊 — an 18% increase from the previous month.
👏 Huge shoutout to 'juroots', our top contributor with 2,746 IOCs submitted.
💀 The most-shared malware family (or in this case framework)? Clearfake, with 2,817 IOCs reported.
Find the full breakdown here: 👉 https://threatfox.abuse.ch/statistics/
#ThreatFox #CommunityPower #SharingIsCaring #CyberThreatIntel