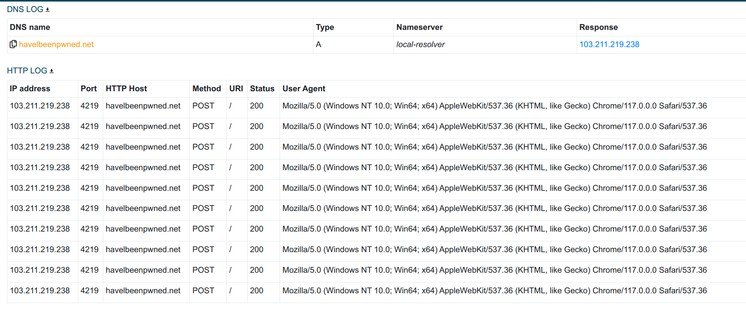
My favorite Remus botnet C2 domain so far 😄
havelbeenpwned .net ⤵️
NICENIC INTERNATIONAL🇨🇳
103.211.219.238:4219⤵️
AS394695 PUBLIC-DOMAIN-REGISTRY 🇮🇳
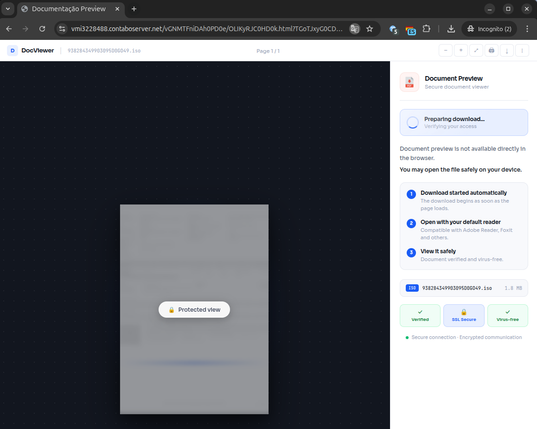
Malware sample:
https://bazaar.abuse.ch/sample/75fce6ec4b0815d7ccc9d87c2687c3c379c8e446739b3302b72688dd632c9f9e/
More #Remnus IOCs available on ThreatFox 🦊
https://threatfox.abuse.ch/browse/malware/win.remus/
/cc @troyhunt