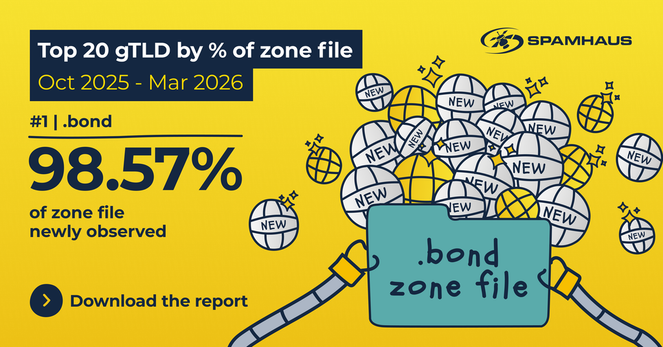
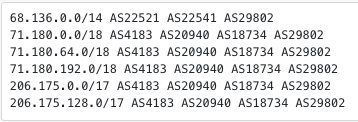
.bond (#6) operated by ShortDot S.A. continues to display patterns of high churn, with new domain registrations (1.13 million) almost equal to its total zone count (1.15 million) - 10–20% of new domains is considered unusually high.
But this reporting period .bond is not alone…
Three quarters of the Top 20 exceed this threshold 😱 - find out which ones in the latest Spamhaus Domain Update:
👉 https://www.spamhaus.org/resource-hub/domain-reputation/domain-reputation-update-oct-2025-mar-2026/