#Cyberangriffe #ITSicherheit #DetourDog #HelpTDS #PoisonedDNS #StarFish #StrelaStealer #TXTRecordAbfrage #VexTrioViper https://sc.tarnkappe.info/1b20a1
#Cyberangriffe #ITSicherheit #DetourDog #HelpTDS #PoisonedDNS #StarFish #StrelaStealer #TXTRecordAbfrage #VexTrioViper https://sc.tarnkappe.info/1b20a1
We recently unraveled a mystery involving ~30k infected websites, DNS TXT records, and Strela Stealer #malware distribution. A threat actor who has been around since at least Feb 2020 has evolved to distribute malware through misdirection and a complex relay system, leaving defenders unsure where the actual malware is hosted.
And to top it off, we found that part of the campaigns were sent via REM proxy, another threat actor we track via DNS that leverages compromised MikroTik routers. These campaigns were spam messages targeting #german speakers with malicious .svg files.
The attachments had links pointing to the first stage of the malware -- or did it? It turns out the threat actor, which we track as Detour Dog, is playing mind games. That link actually triggers server-side DNS queries and the fun begins.
Here is the paper: https://blogs.infoblox.com/threat-intelligence/detour-dog-dns-malware-powers-strela-stealer-campaigns/
More nuggets in the replies.
#malware #infostealer #dns #threatintel #cybersecurity #cybercrime #scam #helptds #tds #infosec #infoblox #strelastealer #phishing #spam #remproxy
🚨 Your inbox's invisible enemy: Sophisticated "Strela Stealer" malware is targeting European email users through fake invoices, using advanced techniques to steal Outlook and Thunderbird credentials. Learn how this threat operates and what you can do to protect your sensitive information.
#SecurityLand #CyberSecurity #EmailSecurity #Trustwave #StrelaStealer #Malware #Europe
2025-02-10 (Monday): Social media post on #StrelaStealer I assisted on for my employer at https://www.linkedin.com/posts/unit42_strelastealer-malspam-webdav-activity-7295144078428491776-vyqY/
and https://x.com/Unit42_Intel/status/1889378454287581678
#pcap, email and malware samples at https://malware-traffic-analysis.net/2025/02/10/index.html
Palo Alto Networks Unit 42 on LinkedIn: #strelastealer #malspam #webdav
2025-02-10 (Monday): #StrelaStealer distributed through #malspam targeting EU. Zip attachment contains .js file that retrieves and displays decoy PDF before running StrelaStealer DLL hosted on #WebDAV server. More info at https://bit.ly/3QgxaLr
#StrelaStealer
https://socprime.com/blog/stealthy-strela-stealer-detection/
Stealthy Strela Stealer Detection: Info-Stealing Malware Resurfaces with Enhanced Capabilities to Target Central and Southwestern Europe - SOC Prime
Detect Strela Stealer malware, which uses obfuscated JavaScript and PowerShell commands to evade detection, with Sigma rules from SOC Prime Platform.
🕵️♂️ Phishing attacks are getting smarter! Strela Stealer targets users in Europe, bypassing security with advanced PowerShell obfuscation and region-specific tactics.
🛡️ Pro Tip: Never open attachments from unknown senders—especially ZIP files disguised as invoices. Phishing simulations can help boost your resilience!
📢 How vigilant are you about verifying unexpected attachments? Share your thoughts!
Read more on how to defend against threats like Strela Stealer: https://guardiansofcyber.com/cybersecurity-news/strela-stealer-powershell-bypass-security-eu/
#Cybersecurity #GuardiansOfCyber #Phishing #DataProtection #StrelaStealer #PhishingAwareness #SecurityTips #OnlineSafety #StaySafe #Guardians
https://www.golem.de/news/angriffe-auf-deutschland-malware-meidet-infektion-russischer-systeme-2406-186424.html #Cybercrime #Malware #Strelastealer
Resurgent malware targets Outlook and Thunderbird users but bypasses Russia⤵️
#malware #cybersecurity #StrelaStealer #infosec
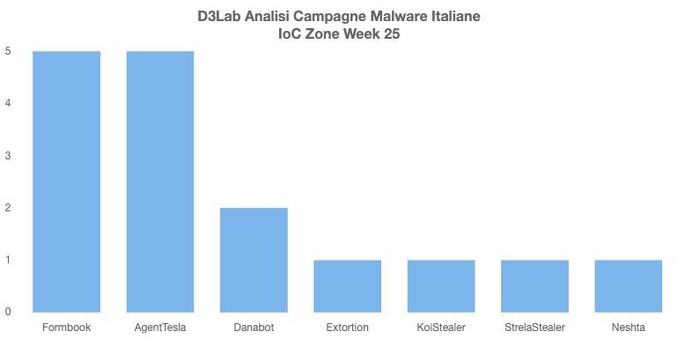
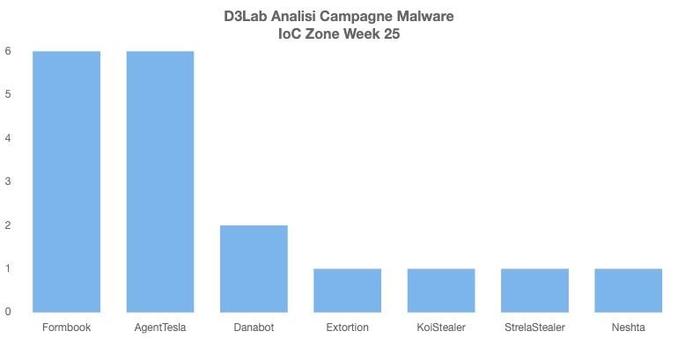
Campagne #Malware #Italy Week 25
☠️💣🔥👻
#Formbook: Pagamento
#AgentTesla: Ordine
#DanaBot: AgenziaEntrate
#KoiLoader - #KoiStealer: Resend
#StrelaStealer: Pagamenti
#Neshta: Ordini