Gigantic 'hole' in the sun wid...
Gigantic 'hole' in the sun wid...
Two giant holes opened up on Sun potentially sending million mph winds to Earth | indy100
https://www.indy100.com/science-tech/sun-hole-solar-winds-earth-2659713729
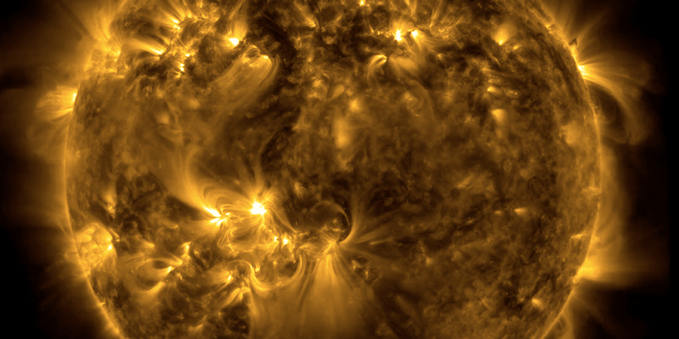
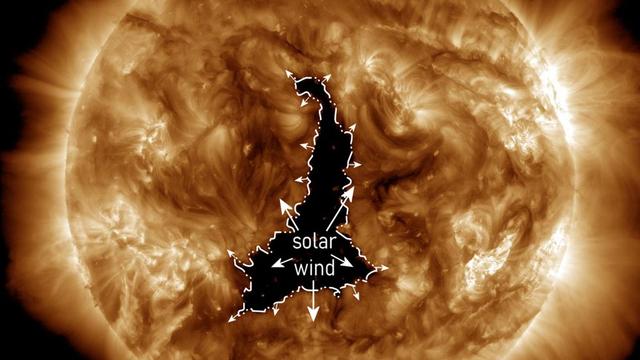
Two giant holes opened up on Sun potentially sending million mph winds to Earth
A giant hole has opened up on the surface of the Sun, which could soon result in solar winds measuring millions of miles per hour hurtling towards Earth.The coronal hole measures 20 times larger than our planet and it’s the second of its type to be detected in the last week. The solar winds will imp...
Nachdem es in den letzten Jahren Angriffe auf #Solarwinds oder #Kaseya gab, steht immer stärker auch die #Opensource Community im Fokus von #Cybercrime, indem durch die Kompromittierung einer Maintainer-Identität potenziell Millionen von Entwicklungsumgebungen und CI/CD-Pipelines ebenfalls kompromittiert werden.
So haben haben Angreifer die #JavaScript-Bibliothek #Axios, eine der meistgenutzten Komponenten moderner Webentwicklung, zeitweise mit #Schadsoftware bestückt:
https://www.it-daily.net/shortnews/npm-bibliothek-axios-zeitweise-mit-malware-verseucht
On that note, #Windows10 should be forcefully open sourced so that the world can decide wether or not #Micorsoft still gets to screw with the NT kernel and userland - as they are want to do.
I keep telling people, it's not the flock - but the shepard. Let's not kid ourselves. #SolarWinds is still reeling in my head. "So you spat unverified code into ring 0? Omg".
The alternative is of course: switch everyone to #Linux, so that #Ableton will port Live and I can leave all this all behind.
The Solar Wind Supply Chain attack
https://negativepid.blog/the-solarwinds-supply-chain-attack/
#SolarWinds #hackers #patching #supplyChain #Cybersecurity #cyberattacks #cyberThreats #onlineSecurity #negativepid
https://securityaffairs.com/189172/security/u-s-cisa-adds-ivanti-epm-solarwinds-and-omnissa-workspace-one-flaws-to-its-known-exploited-vulnerabilities-catalog.html
#securityaffairs #hacking
CVE Alert: CVE-2025-26399 - SolarWinds - Web Help Desk - https://www.redpacketsecurity.com/cve-alert-cve-2025-26399-solarwinds-web-help-desk/
#OSINT #ThreatIntel #CyberSecurity #cve-2025-26399 #solarwinds #web-help-desk
The Solar Wind Supply Chain attack
https://negativepid.blog/the-solarwinds-supply-chain-attack/
#SolarWinds #hackers #patching #supplyChain #Cybersecurity #cyberattacks #cyberThreats #onlineSecurity #negativepid
latest SolarWinds CVEs.. all critical lmao.. patch patch patch!
CVE-2025-40538 - Improper Privilege Management
CVE-2025-40539 - Incorrect Type Conversion or Cast
CVE-2025-40540 - Incorrect Type Conversion or Cast
CVE-2025-40541 - Incorrect Type Conversion or Cast & Authorization Bypass Through User-Controlled Key
SolarWinds Serv-U 15.5.3 and prior versions
Security Advisory Summary:
SolarWinds Serv-U 15.5.4 patches four critical vulnerabilities:
• CVE-2025-40538 – Broken access control → system admin creation + root RCE
• Two type confusion flaws → root code execution
• One IDOR vulnerability → elevated execution
Attack prerequisites:
High-privileged access required. Exploitation likely via credential compromise or chained privilege escalation.
Exposure landscape:
12K+ internet-facing instances observed (Shodan)
File transfer platforms remain ransomware-favored entry vectors
Historical context:
Prior Serv-U CVEs exploited by ransomware groups and state-aligned actors.
Immediate actions:
- Patch to 15.5.4
- Audit privileged accounts
- Review FTP/SFTP exposure
- Monitor for anomalous admin creation
Follow us for tactical advisories and vulnerability intelligence.
Comment with your detection or hardening recommendations.
#Infosec #SolarWinds #ThreatIntel #CVE2025 #RCE #PrivilegeEscalation #BlueTeam #SecurityEngineering #AttackSurface #ZeroTrust